Reading view
Appeals court temporarily pauses order blocking Perplexity’s AI shopping agent on Amazon
A federal appeals court has temporarily put on hold a California judge’s order that would have blocked Perplexity AI from using an AI-powered shopping agent on Amazon, as the case moves forward in a dispute over who controls automated activity inside customer accounts.
The Ninth U.S. Circuit Court of Appeals on Monday granted Perplexity an administrative stay, pausing the injunction while the court considers the company’s request for a longer pause during its appeal. The lower-court order had been set to take effect within days.
Amazon sued Perplexity in November, alleging the startup’s Comet browser and associated AI agent accessed password-protected portions of Amazon customer accounts without Amazon’s authorization, even when users allowed the tool to act for them. Amazon also accused Perplexity of disguising automated activity as human browsing and of ignoring repeated demands to stop.
U.S. District Judge Maxine Chesney in San Francisco granted Amazon’s request for a preliminary injunction on March 9. She wrote that Amazon was likely to succeed on claims under the federal Computer Fraud and Abuse Act and California’s Comprehensive Computer Data Access and Fraud Act. Chesney said Amazon had provided strong evidence that Perplexity accessed accounts “with the Amazon user’s permission but without authorization by Amazon.”
Chesney’s order required Perplexity to prohibit Comet from accessing or attempting to access Amazon user accounts, and to delete Amazon accounts and customer data it collected. Chesney also cited Amazon’s evidence of response costs, including employee time spent developing tools to block Comet and detect future access, writing that the company incurred more than the threshold amount often used to support computer-fraud claims.
Perplexity argues the activity is lawful because users authorized the AI agent to make purchases and navigate the site on their behalf. In seeking a pause, the company said blocking its product from one of the internet’s largest shopping sites would cause “devastating harm” to the business and to consumers.
A Perplexity spokesperson told CyberScoop Tuesday the company would continue to fight for “people’s right to choose their own AI.” Amazon declined to comment.
The case underscores issues with “agentic” AI tools that move from answering questions to initiating transactions. Courts are being asked to weigh user permission against platform authorization, and to decide whether automated representatives must follow platform rules designed to limit undisclosed bots in sensitive account areas.
The post Appeals court temporarily pauses order blocking Perplexity’s AI shopping agent on Amazon appeared first on CyberScoop.
Is Your Android TV Streaming Box Part of a Botnet?
On the surface, the Superbox media streaming devices for sale at retailers like BestBuy and Walmart may seem like a steal: They offer unlimited access to more than 2,200 pay-per-view and streaming services like Netflix, ESPN and Hulu, all for a one-time fee of around $400. But security experts warn these TV boxes require intrusive software that forces the user’s network to relay Internet traffic for others, traffic that is often tied to cybercrime activity such as advertising fraud and account takeovers.
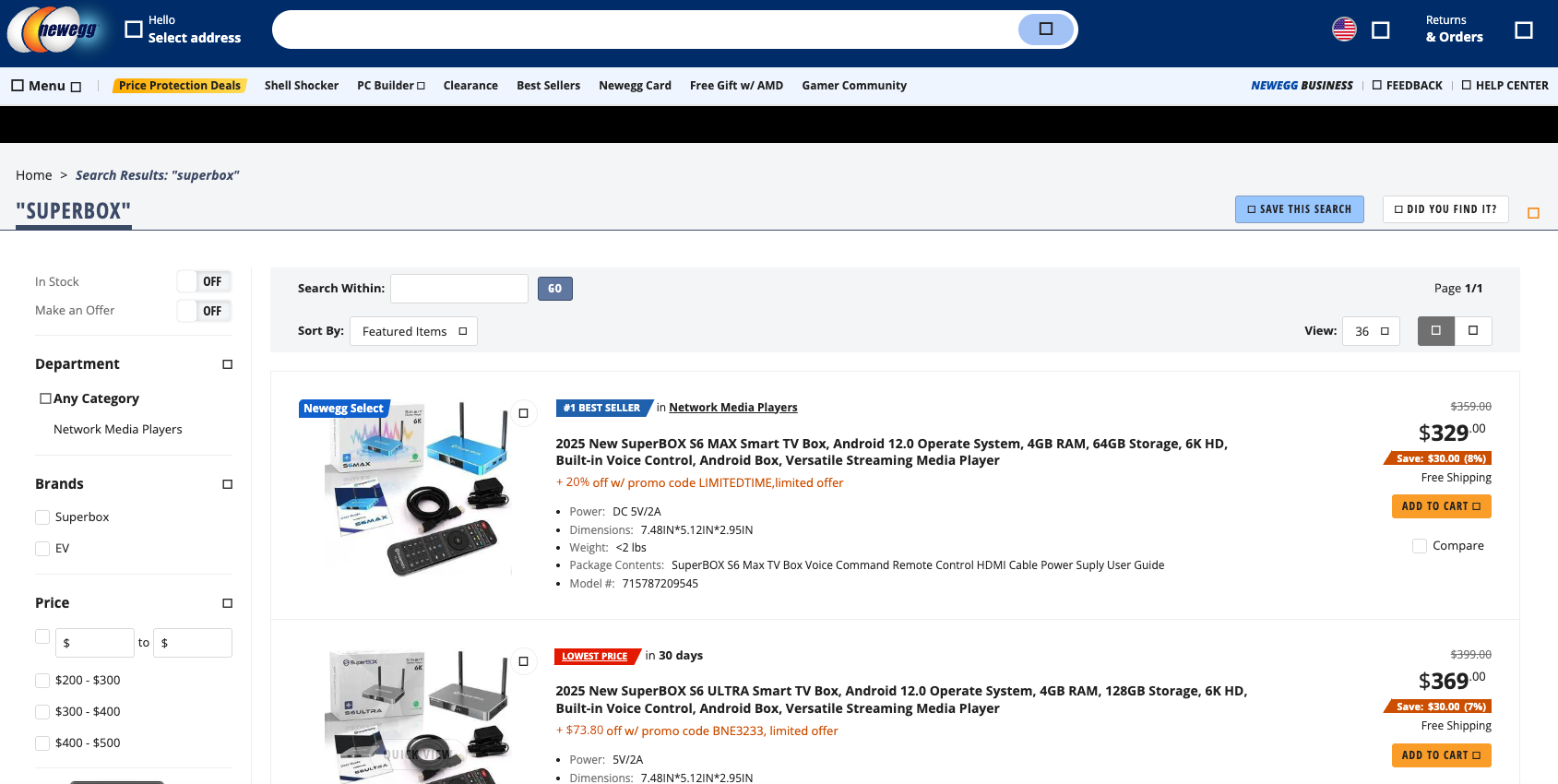
Superbox media streaming boxes for sale on Walmart.com.
Superbox bills itself as an affordable way for households to stream all of the television and movie content they could possibly want, without the hassle of monthly subscription fees — for a one-time payment of nearly $400.
“Tired of confusing cable bills and hidden fees?,” Superbox’s website asks in a recent blog post titled, “Cheap Cable TV for Low Income: Watch TV, No Monthly Bills.”
“Real cheap cable TV for low income solutions does exist,” the blog continues. “This guide breaks down the best alternatives to stop overpaying, from free over-the-air options to one-time purchase devices that eliminate monthly bills.”
Superbox claims that watching a stream of movies, TV shows, and sporting events won’t violate U.S. copyright law.
“SuperBox is just like any other Android TV box on the market, we can not control what software customers will use,” the company’s website maintains. “And you won’t encounter a law issue unless uploading, downloading, or broadcasting content to a large group.”
A blog post from the Superbox website.
There is nothing illegal about the sale or use of the Superbox itself, which can be used strictly as a way to stream content at providers where users already have a paid subscription. But that is not why people are shelling out $400 for these machines. The only way to watch those 2,200+ channels for free with a Superbox is to install several apps made for the device that enable them to stream this content.
Superbox’s homepage includes a prominent message stating the company does “not sell access to or preinstall any apps that bypass paywalls or provide access to unauthorized content.” The company explains that they merely provide the hardware, while customers choose which apps to install.
“We only sell the hardware device,” the notice states. “Customers must use official apps and licensed services; unauthorized use may violate copyright law.”
Superbox is technically correct here, except for maybe the part about how customers must use official apps and licensed services: Before the Superbox can stream those thousands of channels, users must configure the device to update itself, and the first step involves ripping out Google’s official Play store and replacing it with something called the “App Store” or “Blue TV Store.”
Superbox does this because the device does not use the official Google-certified Android TV system, and its apps will not load otherwise. Only after the Google Play store has been supplanted by this unofficial App Store do the various movie and video streaming apps that are built specifically for the Superbox appear available for download (again, outside of Google’s app ecosystem).
Experts say while these Android streaming boxes generally do what they advertise — enabling buyers to stream video content that would normally require a paid subscription — the apps that enable the streaming also ensnare the user’s Internet connection in a distributed residential proxy network that uses the devices to relay traffic from others.
Ashley is a senior solutions engineer at Censys, a cyber intelligence company that indexes Internet-connected devices, services and hosts. Ashley requested that only her first name be used in this story.
In a recent video interview, Ashley showed off several Superbox models that Censys was studying in the malware lab — including one purchased off the shelf at BestBuy.
“I’m sure a lot of people are thinking, ‘Hey, how bad could it be if it’s for sale at the big box stores?'” she said. “But the more I looked, things got weirder and weirder.”
Ashley said she found the Superbox devices immediately contacted a server at the Chinese instant messaging service Tencent QQ, as well as a residential proxy service called Grass IO.
GET GRASSED
Also known as getgrass[.]io, Grass says it is “a decentralized network that allows users to earn rewards by sharing their unused Internet bandwidth with AI labs and other companies.”
“Buyers seek unused internet bandwidth to access a more diverse range of IP addresses, which enables them to see certain websites from a retail perspective,” the Grass website explains. “By utilizing your unused internet bandwidth, they can conduct market research, or perform tasks like web scraping to train AI.” 
Reached via Twitter/X, Grass founder Andrej Radonjic told KrebsOnSecurity he’d never heard of a Superbox, and that Grass has no affiliation with the device maker.
“It looks like these boxes are distributing an unethical proxy network which people are using to try to take advantage of Grass,” Radonjic said. “The point of grass is to be an opt-in network. You download the grass app to monetize your unused bandwidth. There are tons of sketchy SDKs out there that hijack people’s bandwidth to help webscraping companies.”
Radonjic said Grass has implemented “a robust system to identify network abusers,” and that if it discovers anyone trying to misuse or circumvent its terms of service, the company takes steps to stop it and prevent those users from earning points or rewards.
Superbox’s parent company, Super Media Technology Company Ltd., lists its street address as a UPS store in Fountain Valley, Calif. The company did not respond to multiple inquiries.
According to this teardown by behindmlm.com, a blog that covers multi-level marketing (MLM) schemes, Grass’s compensation plan is built around “grass points,” which are earned through the use of the Grass app and through app usage by recruited affiliates. Affiliates can earn 5,000 grass points for clocking 100 hours usage of Grass’s app, but they must progress through ten affiliate tiers or ranks before they can redeem their grass points (presumably for some type of cryptocurrency). The 10th or “Titan” tier requires affiliates to accumulate a whopping 50 million grass points, or recruit at least 221 more affiliates.
Radonjic said Grass’s system has changed in recent months, and confirmed the company has a referral program where users can earn Grass Uptime Points by contributing their own bandwidth and/or by inviting other users to participate.
“Users are not required to participate in the referral program to earn Grass Uptime Points or to receive Grass Tokens,” Radonjic said. “Grass is in the process of phasing out the referral program and has introduced an updated Grass Points model.”
A review of the Terms and Conditions page for getgrass[.]io at the Wayback Machine shows Grass’s parent company has changed names at least five times in the course of its two-year existence. Searching the Wayback Machine on getgrass[.]io shows that in June 2023 Grass was owned by a company called Wynd Network. By March 2024, the owner was listed as Lower Tribeca Corp. in the Bahamas. By August 2024, Grass was controlled by a Half Space Labs Limited, and in November 2024 the company was owned by Grass OpCo (BVI) Ltd. Currently, the Grass website says its parent is just Grass OpCo Ltd (no BVI in the name).
Radonjic acknowledged that Grass has undergone “a handful of corporate clean-ups over the last couple of years,” but described them as administrative changes that had no operational impact. “These reflect normal early-stage restructuring as the project moved from initial development…into the current structure under the Grass Foundation,” he said.
UNBOXING
Censys’s Ashley said the phone home to China’s Tencent QQ instant messaging service was the first red flag with the Superbox devices she examined. She also discovered the streaming boxes included powerful network analysis and remote access tools, such as Tcpdump and Netcat.
“This thing DNS hijacked my router, did ARP poisoning to the point where things fall off the network so they can assume that IP, and attempted to bypass controls,” she said. “I have root on all of them now, and they actually have a folder called ‘secondstage.’ These devices also have Netcat and Tcpdump on them, and yet they are supposed to be streaming devices.”
A quick online search shows various Superbox models and many similar Android streaming devices for sale at a wide range of top retail destinations, including Amazon, BestBuy, Newegg, and Walmart. Newegg.com, for example, currently lists more than three dozen Superbox models. In all cases, the products are sold by third-party merchants on these platforms, but in many instances the fulfillment comes from the e-commerce platform itself.
“Newegg is pretty bad now with these devices,” Ashley said. “Ebay is the funniest, because they have Superbox in Spanish — the SuperCaja — which is very popular.”
Ashley said Amazon recently cracked down on Android streaming devices branded as Superbox, but that those listings can still be found under the more generic title “modem and router combo” (which may be slightly closer to the truth about the device’s behavior).
Superbox doesn’t advertise its products in the conventional sense. Rather, it seems to rely on lesser-known influencers on places like Youtube and TikTok to promote the devices. Meanwhile, Ashley said, Superbox pays those influencers 50 percent of the value of each device they sell.
“It’s weird to me because influencer marketing usually caps compensation at 15 percent, and it means they don’t care about the money,” she said. “This is about building their network.”

A TikTok influencer casually mentions and promotes Superbox while chatting with her followers over a glass of wine.
BADBOX
As plentiful as the Superbox is on e-commerce sites, it is just one brand in an ocean of no-name Android-based TV boxes available to consumers. While these devices generally do provide buyers with “free” streaming content, they also tend to include factory-installed malware or require the installation of third-party apps that engage the user’s Internet address in advertising fraud.
In July 2025, Google filed a “John Doe” lawsuit (PDF) against 25 unidentified defendants dubbed the “BadBox 2.0 Enterprise,” which Google described as a botnet of over ten million Android streaming devices that engaged in advertising fraud. Google said the BADBOX 2.0 botnet, in addition to compromising multiple types of devices prior to purchase, can also infect devices by requiring the download of malicious apps from unofficial marketplaces.

Some of the unofficial Android devices flagged by Google as part of the Badbox 2.0 botnet are still widely for sale at major e-commerce vendors. Image: Google.
Several of the Android streaming devices flagged in Google’s lawsuit are still for sale on top U.S. retail sites. For example, searching for the “X88Pro 10” and the “T95” Android streaming boxes finds both continue to be peddled by Amazon sellers.
Google’s lawsuit came on the heels of a June 2025 advisory from the Federal Bureau of Investigation (FBI), which warned that cyber criminals were gaining unauthorized access to home networks by either configuring the products with malicious software prior to the user’s purchase, or infecting the device as it downloads required applications that contain backdoors, usually during the set-up process.
“Once these compromised IoT devices are connected to home networks, the infected devices are susceptible to becoming part of the BADBOX 2.0 botnet and residential proxy services known to be used for malicious activity,” the FBI said.
The FBI said BADBOX 2.0 was discovered after the original BADBOX campaign was disrupted in 2024. The original BADBOX was identified in 2023, and primarily consisted of Android operating system devices that were compromised with backdoor malware prior to purchase.
Riley Kilmer is founder of Spur, a company that tracks residential proxy networks. Kilmer said Badbox 2.0 was used as a distribution platform for IPidea, a China-based entity that is now the world’s largest residential proxy network.
Kilmer and others say IPidea is merely a rebrand of 911S5 Proxy, a China-based proxy provider sanctioned last year by the U.S. Department of the Treasury for operating a botnet that helped criminals steal billions of dollars from financial institutions, credit card issuers, and federal lending programs (the U.S. Department of Justice also arrested the alleged owner of 911S5).
How are most IPidea customers using the proxy service? According to the proxy detection service Synthient, six of the top ten destinations for IPidea proxies involved traffic that has been linked to either ad fraud or credential stuffing (account takeover attempts).
Kilmer said companies like Grass are probably being truthful when they say that some of their customers are companies performing web scraping to train artificial intelligence efforts, because a great deal of content scraping which ultimately benefits AI companies is now leveraging these proxy networks to further obfuscate their aggressive data-slurping activity. By routing this unwelcome traffic through residential IP addresses, Kilmer said, content scraping firms can make it far trickier to filter out.
“Web crawling and scraping has always been a thing, but AI made it like a commodity, data that had to be collected,” Kilmer told KrebsOnSecurity. “Everybody wanted to monetize their own data pots, and how they monetize that is different across the board.”
SOME FRIENDLY ADVICE
Products like Superbox are drawing increased interest from consumers as more popular network television shows and sportscasts migrate to subscription streaming services, and as people begin to realize they’re spending as much or more on streaming services than they previously paid for cable or satellite TV.
These streaming devices from no-name technology vendors are another example of the maxim, “If something is free, you are the product,” meaning the company is making money by selling access to and/or information about its users and their data.
Superbox owners might counter, “Free? I paid $400 for that device!” But remember: Just because you paid a lot for something doesn’t mean you are done paying for it, or that somehow you are the only one who might be worse off from the transaction.
It may be that many Superbox customers don’t care if someone uses their Internet connection to tunnel traffic for ad fraud and account takeovers; for them, it beats paying for multiple streaming services each month. My guess, however, is that quite a few people who buy (or are gifted) these products have little understanding of the bargain they’re making when they plug them into an Internet router.
Superbox performs some serious linguistic gymnastics to claim its products don’t violate copyright laws, and that its customers alone are responsible for understanding and observing any local laws on the matter. However, buyer beware: If you’re a resident of the United States, you should know that using these devices for unauthorized streaming violates the Digital Millennium Copyright Act (DMCA), and can incur legal action, fines, and potential warnings and/or suspension of service by your Internet service provider.
According to the FBI, there are several signs to look for that may indicate a streaming device you own is malicious, including:
-The presence of suspicious marketplaces where apps are downloaded.
-Requiring Google Play Protect settings to be disabled.
-Generic TV streaming devices advertised as unlocked or capable of accessing free content.
-IoT devices advertised from unrecognizable brands.
-Android devices that are not Play Protect certified.
-Unexplained or suspicious Internet traffic.
This explainer from the Electronic Frontier Foundation delves a bit deeper into each of the potential symptoms listed above.
Amazon warns of global rise in specialized cyber-enabled kinetic targeting
Amazon said the lines between cyberattacks and physical, real-world attacks are blurring quickly — prompting the tech giant to call for a new category of warfare: cyber-enabled kinetic targeting.
Nation-states have combined and understood how logical systems and the physical world interact for a long time, but more non-traditional attackers are showcasing expertise in using cyberattacks to enable and amplify the impact of kinetic military operations, according to Amazon Threat Intelligence.
“The collective industry and our customers have to really pay attention to this and change the way we’re doing things,” Steve Schmidt, chief security officer at Amazon, told CyberScoop in a phone interview. “Physical and digital security cannot be treated as separate domains with separate domains and approaches.”
Governments traditionally have requirements for actions to occur or access to specific information, and oftentimes those objectives were treated separately. Yet, now when governments want to achieve military objectives, military planners are asking for more precise details about the target, Schmidt said.
While nation-state attackers can compromise networks that contain data identifying those targets, those details are typically generalized. To get more exact information, nation-state attackers are compromising closed-circuit television (CCTV), or security cameras, on the target itself.
This allows military planners to “see where the [target] is physically and actually do live adjustments of targeting while you have weapons in flight,” Schmidt said.
Amazon provided two case studies as examples of cyber-enabled kinetic targeting in a blog post Wednesday. The most recent attack involves MuddyWater, a threat group linked to Iran’s Ministry of Intelligence and Security, that provisioned a server in May and used that infrastructure a month later to access another compromised server containing live CCTV streams from Jerusalem.
When Iran launched missile attacks on Jerusalem on June 23, Israeli authorities said Iranian forces were using real-time intelligence from compromised security cameras to adjust missile targeting, Amazon said.
Cyber-enabled kinetic targeting employs common tools and tactics that display advanced skills in anonymizing virtual private networks, using their own servers for command-and-control capabilities, compromising enterprise systems such as CCTV systems or maritime platforms, and gaining access to real-time data streams, according to Amazon.
These multi-layered, collaborative attacks require critical infrastructure operators and threat intelligence professionals to expand their remit, Schmidt said.
“Traditional cybersecurity frameworks treat the digital and the physical threats as really separate domains, but we realized, through our own internal work and our research, of course, that this separation is not only artificial but actually detrimental,” he said.
“You have to think about these things as integrated wholes, because even physical world assets, like a ship, are really a cyber asset as well. And multiple nation-state threat groups are pioneering a new operational model where cyber reconnaissance directly enables kinetic targeting,” Schmidt added.
Amazon said this is a warning and call to action for defenders to consider how compromised systems might be used to support physical attacks and recognize that their systems might be valuable targeting aids for kinetic operations. This also demonstrates the need for threat intelligence sharing across the private sector and government to work through more complex attribution response frameworks, the company said.
Multiple nation-states will increasingly employ cyber-enabled kinetic targeting, CJ Moses, chief information security officer of Amazon Integrated Security, said in the blog post.
“Nation-state actors are recognizing the force multiplier effect of combining digital reconnaissance with physical attacks,” he said. “This trend represents a fundamental evolution in warfare, where the traditional boundaries between cyber and kinetic operations are dissolving.”
Many seemingly espionage-focused attacks that have already been made public might ultimately be an entry point for kinetic targeting, according to Schmidt.
Countries that have both advanced cyber capabilities and military strength are most likely to succeed at cyber-enabled kinetic targeting, he said.
The most prominent threats come from nation-state attackers who are more specialized in their targeting. “The targeting of maritime navigation systems is a relatively unique skill, and it is different from the targeting of a cryptocurrency exchange,” Schmidt said.
“It takes different knowledge, and so you’re seeing groups pop up onto the radar, which we may not have followed before because there wasn’t that volume of activity.”
The post Amazon warns of global rise in specialized cyber-enabled kinetic targeting appeared first on CyberScoop.
Amazon pins Cisco, Citrix zero-day attacks to APT group
Amazon’s threat intelligence team said it observed an advanced persistent threat group exploiting zero-day vulnerabilities affecting Cisco Identity Service Engine and Citrix NetScaler products before the vendors disclosed and patched the defects last summer.
Amazon’s MadPot honeypot service detected active exploitation of the critical defects — CVE-2025-5777 in Citrix and CVE-2025-20337 in Cisco — and through further investigation determined a highly resourced threat actor was behind the attacks, CJ Moses, chief information security officer of Amazon Integrated Security, said in a blog post Wednesday.
“We assess with high confidence it was the same threat actor observed exploiting both vulnerabilities,” Moses told CyberScoop in an email.
Amazon said its discovery reinforced multiple trends afoot, including threat groups’ increased focus on identity and network edge infrastructure and their ability to quickly weaponize vulnerabilities as zero-days before vendors disclose or patch defects in their products.
The origins and identity of the threat group behind the attacks remains unknown, yet Moses said “prolonged access to the target for espionage is the most likely objective.”
Amazon threat researchers said the threat group used custom malware with a backdoor specifically designed for Cisco ISE environments that demonstrated advanced evasion techniques. “The threat actor’s custom tooling demonstrated a deep understanding of enterprise Java applications, Tomcat internals and the specific architectural nuances of the Cisco ISE,” Moses said in the blog post.
Cisco disclosed CVE-2025-20337 on June 25, yet Amazon said exploitation was already underway in May. Amazon discovered the pre-disclosure exploits in early July and traced attacks back to May and June, Moses said.
Amazon disclosed active exploitation of the defect to Cisco, which informed its customers of the issue within hours, Moses added. He did not share information about how many organizations have been impacted by CVE-2025-20337 exploits.
Citrix disclosed CVE-2025-5777, also known as CitrixBleed 2 due to striking similarities with a 2023 defect in the same products, on June 17. The Cybersecurity and Infrastructure Security Agency added the exploit to its known exploited vulnerabilities catalog on July 10.
By mid-July, researchers had observed more than 11.5 million attack attempts, targeting thousands of sites since the exploit was disclosed.
Amazon declined to explain why it’s sharing information about active zero-day exploitation of the Cisco and Citrix defects months later, and the company said it doesn’t have additional information about more recent attacks linked to the vulnerabilities.
Moses noted the threat group’s use of multiple zero-day exploits indicates the attackers have advanced vulnerability research capabilities or access to undisclosed vulnerability information.
The post Amazon pins Cisco, Citrix zero-day attacks to APT group appeared first on CyberScoop.
Amazon rolls out AI bug bounty program
Amazon became the latest company to open its large language models to outside security researchers, announcing the creation of a new bug bounty program for the tech giant’s AI tools.
The program will allow select third-party researchers and academic teams to prod NOVA, Amazon’s suite of foundational AI models and receive compensation for their findings. It will cover a range of common vulnerabilities that affect most generative AI systems: prompt injection, jailbreaking and vulnerabilities within the model that have “real-world exploitation potential.” Researchers will also look at how the models could be manipulated to assist in the production of chemical, biological, radiological and nuclear weapons.
“Security researchers are the ultimate real-world validators that our AI models and applications are holding up under creative scrutiny,” Hudson Thrift, CISO of Amazon Stores, said in a statement Tuesday.
Participants will be selected next year by Amazon through an invite-only system, meaning the company will still retain influence over which security researchers get access to their technology. According to the company, it has paid out more than $55,000 to researchers for 30 validated AI-related vulnerabilities under its broader public bug bounty program.
Amazon has bet big on generative AI, developing its own family of commercial large language models (NOVA) while also providing services like Amazon Bedrock that allow customers to access models from other companies like Anthropic, Mistral AI and others.
But as these products have become increasingly integrated within Amazon and user organizations, their safety and security has come with higher stakes and larger potential downstream effects.
“As Nova models power a growing ecosystem across Alexa, AWS customers through Amazon Bedrock, and other Amazon products, ensuring their security remains an essential focus,” Amazon wrote in the announcement, adding “By creating opportunities for hands-on learning and discovery, Amazon is helping raise a new generation of researchers equipped to secure the systems that will define the next era of AI.”
Earlier this year, Amazon held a tournament between 10 university research teams to find bugs and vulnerabilities in Amazon’s coding AI models. Each team received $250,000 and AWS credits upfront to conduct their work, while winners pulled in an additional $700,000 in reward money, according to the company.Their findings included novel bugs and methods for jailbreaking, safety alignment, data poisoning attacks and discovered a number of tradeoffs between security and functionality within Amazon’s NOVA models.
The post Amazon rolls out AI bug bounty program appeared first on CyberScoop.
With each cloud outage, calls for government action grow louder
When a pair of high-profile internet outages took down large chunks of the internet last month, the events briefly brought hundreds of organizations to a near-halt and prevented millions of users from accessing core services for everyday business needs.
From Starbucks to crypto exchanges to the messaging app Signal, the outages rippled across nearly every sector, shining a spotlight onto the country’s — and even the government’s — reliance on a mere handful of cloud service providers.
In the wake of those incidents, watchdog groups are calling on federal regulators to scrutinize the role that massive cloud companies like Amazon and Microsoft play in owning and maintaining much of our collective backend IT infrastructure.
Meanwhile, technology and cybersecurity experts point out that, because of financial and business realities, there are very few alternatives to the large companies that now dominate the market.
The Amazon Web Services outage began Oct. 19 and lasted into Oct. 20. According to Amazon’s post-mortem, a single software bug in DynamoDB — the system that manages website addresses, along with efforts to repair it — caused all services in the Northern Virginia region that relied on the tool to go down for 15 hours.
Just over a week later, Microsoft’s Azure cloud platform experienced an outage impacting several of its services. According to Microsoft, an “inadvertent tenant configuration change” occurred in Azure Front Door, the company’s content delivery network.
The outages exposed just how fragile the country’s digital infrastructure is and showed the risks of letting a few companies hold so much power. As a result, some groups are urging federal regulators to address the issue.
Concerns over corporate consolidation abound
In a letter to the Federal Trade Commission, a coalition of advocacy groups — including Public Citizen and the Tech Oversight Project — said AWS’s hours-long outage Oct. 19 illustrated the country’s “precarious overreliance” on a small number of CSPs.
“The cloud services market that is foundational to this digital infrastructure is dominated by just a few players, with Amazon dominating the industry. Many firms, financial institutions, telecoms, and government bodies rely on these cloud service providers — and often solely on a single one,” the letter to FTC Chair Andrew Ferguson stated. “That precarious overreliance is compromising our nation’s security and commerce, as the October 19 global outage vividly illustrated. “
The FTC has focused on Amazon’s business practices in prior years. Earlier this year, the agency required the company to pay a $1 billion civil penalty and provide $1.5 billion in refunds to customers as part of a settlement related to its Prime subscription service.
The letter regarding Amazon Web Services, shared first with Scoop News Group, asks Ferguson to explain how the FTC is responding to the specific outage and to the larger economic and security risks.
“We ask you to swiftly conduct a market structure review of leading cloud services providers, including but not limited to Amazon, to assess how their market dominance and use of monopoly power to stifle competition is creating systemic fragility across industries,” the letter stated.
The groups asked that the probe cover the dependencies that critical infrastructure sectors like telecommunication and government services have on any single cloud provider, along with the risks this could have on data security, privacy and consumer protection.
Other signatories to the letter include the Center for Economic Integrity, the American Economic Liberties Project, and NextGen Competition, among others. The FTC did not respond to a request for comment.
The reality of consolidated cloud infrastructure
The advocacy letter comes as technology and cybersecurity experts have raised similar concerns about a few companies controlling most of the internet’s infrastructure.
Meredith Whittaker, CEO of Signal, said users were surprised to learn that the encrypted messaging app ran partly on AWS infrastructure — but she believes they shouldn’t have been.
She explained in a post on Bluesky that the surprise from users “indicates that the extent of the concentration of power in the hands of a few hyperscalers is way less widely understood than I’d assumed.”
Whittaker pointed out that the reality for Signal — and virtually every other online business — is that running these services requires extremely expensive infrastructure and specialized expertise to work as intended. Those resources are almost entirely concentrated among large corporations with the money and capacity to support and sustain such infrastructure.
Instead of managing their own data centers, many companies and federal agencies have simply been “renting capacity” from Amazon, Microsoft and others, according to Benjamin Lee, a computer and information science professor at the University of Pennsylvania.
“All of that is very efficient. Much more efficient than what individual or private companies or smaller data centers can do,” Lee said. “With so much compute moving into the cloud, that has created, to some extent, a single point of failure.”
Amazon’s post-mortem essentially speaks to that consolidation, detailing a dizzying array of different data center clusters, technologies, hardware, bespoke tooling and expertise across multiple internet domains that can’t be easily duplicated without tremendous resources.
“The question isn’t ‘why does Signal use AWS?’” Whittaker wrote on Bluesky. “It’s to look at the infrastructure requirements of any global, real-time mass comms platform and ask how is it that we got to a place where there’s no realistic alternative to AWS and the other hyperscalers?”
One expert, a senior architect and cybersecurity adviser who works with hyperscalers, endorsed Whittaker’s points about the private sector’s collective reliance on Amazon, Microsoft and other hyperscale cloud companies.
However, the executive, who requested anonymity to candidly discuss their work, noted that there are few organizations capable of duplicating these backend functions at scale while remaining profitable.
Indeed, part of the market dominance companies like AWS enjoy is also because they’re able to process massive volumes of internet and financial transactions that underpin billions of dollars of economic activity every day.
“Sometimes when something like this happens, there’s a bunch of backseat, Monday-morning-quarterback types that are like, ‘oh, you know, if this were me and it was my data center,’” the executive said.
“First of all, stop: Your data center can have maintenance windows like 6 a.m. on Sunday morning,” they continued. “These guys can’t; they don’t have outages. They are built at a scale that is staggering.”
That argument was shared by Nicholas Weaver, a senior researcher focused on network security at the International Computer Science Institute, who said that the relative rarity of major outages like the kind experienced by AWS and Azure in recent weeks is the exception that proves the rule.
“Being down for 6 hours once every 2 years+ is damn near [perfect] reliability (99.99% uptime),” Weaver wrote about AWS. “Certainly 10x better than the edge network I use to connect to it.”
The hyperscaler adviser largely agreed with that perspective, telling Scoop News Group that AWS and Azure handle countless IT tasks for businesses, from backups to security fixes and maintenance. In return for rare outages, companies get instant access to top technology and expertise they couldn’t afford on their own.
“Yeah, our options are limited, but on the other hand I kind of view this as: 10 years ago, I was fine running my own mail server as sort of a hobbyist,” the executive said. “You’d be an idiot to do that today, because you need such deep resources on IP reputation, on anti-DDoS [and other specialties] that you need the cloud players of the world.”
Security gaps exist
Beyond the risks of technical glitches leading to mass outages, some cybersecurity researchers worry that this same complexity could also be exploited by malicious actors to cause widespread internet disruption.
A quarterly threat report released last week by DigiCert, a company that provides validation services for digital certificates like Transport Layer Security (TLS) and Secure Socket Layer (SSL), looked at trillions of network events across their different platforms and noted that large-scale disruptive attacks targeting internet infrastructure appears to be getting more common.
Between July and August, the company faced two distributed-denial-of-service attacks with massive, “tsunami”-like scale: one flooded traffic at 2.4 terabits per second while the other topped out at 3.7 terabits per second.
Michael Smith, DigiCert’s chief technology officer for application security, said that “while most DNS activity remains healthy, operational anomalies surfaced at scale.”
“These anomalies — typically caused by misconfigured resolvers or automated scanning but sometimes a symptom of scanning or an attack — highlight how small inefficiencies can ripple globally through interconnected systems,” he added.
Meanwhile, the U.S. continues to struggle with Chinese hackers infiltrating its critical infrastructure. Many U.S. officials and experts worry China could launch cyberattacks if the U.S. responds to a potential invasion of Taiwan. The small number of tech companies responsible for the cloud ecosystem could be a target for malicious hackers in an effort to cause prolonged widespread outages.
How an outage could impact federal agencies
The letter to the FTC also raised concerns about government agencies’ potential reliance on cloud service providers, particularly during outages — even as the impact of those outages on federal services remains unclear.
AWS and Microsoft are two of the biggest cloud providers for government agencies. Both companies offer special government cloud services with extra security for sensitive data. For example, AWS has GovCloud and Microsoft has Azure Government — each with regions that are “physically isolated” from their standard commercial cloud systems to better protect government information.
The post-outage report for AWS did not mention GovCloud as one of the impacted regions and the GovCloud online health dashboard shows no disruptions on Oct. 19. An AWS spokesperson later confirmed GovCloud was not impacted.
While GovCloud appeared shielded from impact, speculation swirled online that some federal workers’ functions may still have been affected. A source familiar with the IT government contracting space told Scoop News Group that AWS’s commercial cloud is often used and preferred by federal agencies, even when GovCloud services are offered.
“For standard, civilian government use cases and workloads, there’s frankly not a compelling reason to use GovCloud most of the time,” the source said, speaking on the condition of anonymity. “It’s more expensive and has fewer features than the commercial offering, and updates to common features happen sometimes months ahead of GovCloud.”
The four U.S. regions of the standard, commercial AWS cloud have received a Provisional Authority to Operate (P-ATO) at the moderate impact level under FedRAMP. As a result, the commercial version can be used when the work in question does not require the higher compliance levels that GovCloud offers, another source familiar with AWS platforms said.
Like AWS, Microsoft’s Azure Government platform also uses physically isolated data centers and networks in the U.S. only. Microsoft’s preliminary outage report does not include Azure Government on the list of impacted services. When asked about both the corporate consolidation concerns and the government impacts, a Microsoft spokesperson pointed Scoop News Group to the company’s statement about the Oct. 29 outage.
James Rodd, a senior principal cloud architect at SAIC, also speculated that there could be additional security risks since the outage occurred during a government shutdown.
“We happen to be in a very precarious situation right now with the government shutdown, where the agencies that should be watching this are lower-staffed,” said Rodd, who served as an enterprise cloud architect at the Federal Emergency Management Agency for three years before joining SAIC.
Amid speculation over the outages, conversations about corporate consolidation also seeped into the government tech sector.
Timothy Edgar, who served as a national security official in the Obama administration, said the topic is often complicated and requires government oversight. There are “real advantages” to the size of companies like Amazon, including giving customers the ability to “scale up quickly” and gain access to essential cybersecurity tools.
“I wouldn’t say that the fact that there are a few big cloud providers is necessarily a bad thing, but it does create problems with having a big company when something does go wrong,” Edgar said. “Just with any big industry that’s really essential to national security, the government has an important role in holding these industries accountable.”
This story was updated Nov. 5, 2025, to include an AWS response to a request for comment, correct the timing of the Oct. 19-20 AWS outage and clarify that the 2023 FTC antitrust suit was against Amazon’s retail division.
The post With each cloud outage, calls for government action grow louder appeared first on CyberScoop.
Cloudflare Scrubs Aisuru Botnet from Top Domains List
For the past week, domains associated with the massive Aisuru botnet have repeatedly usurped Amazon, Apple, Google and Microsoft in Cloudflare’s public ranking of the most frequently requested websites. Cloudflare responded by redacting Aisuru domain names from their top websites list. The chief executive at Cloudflare says Aisuru’s overlords are using the botnet to boost their malicious domain rankings, while simultaneously attacking the company’s domain name system (DNS) service.
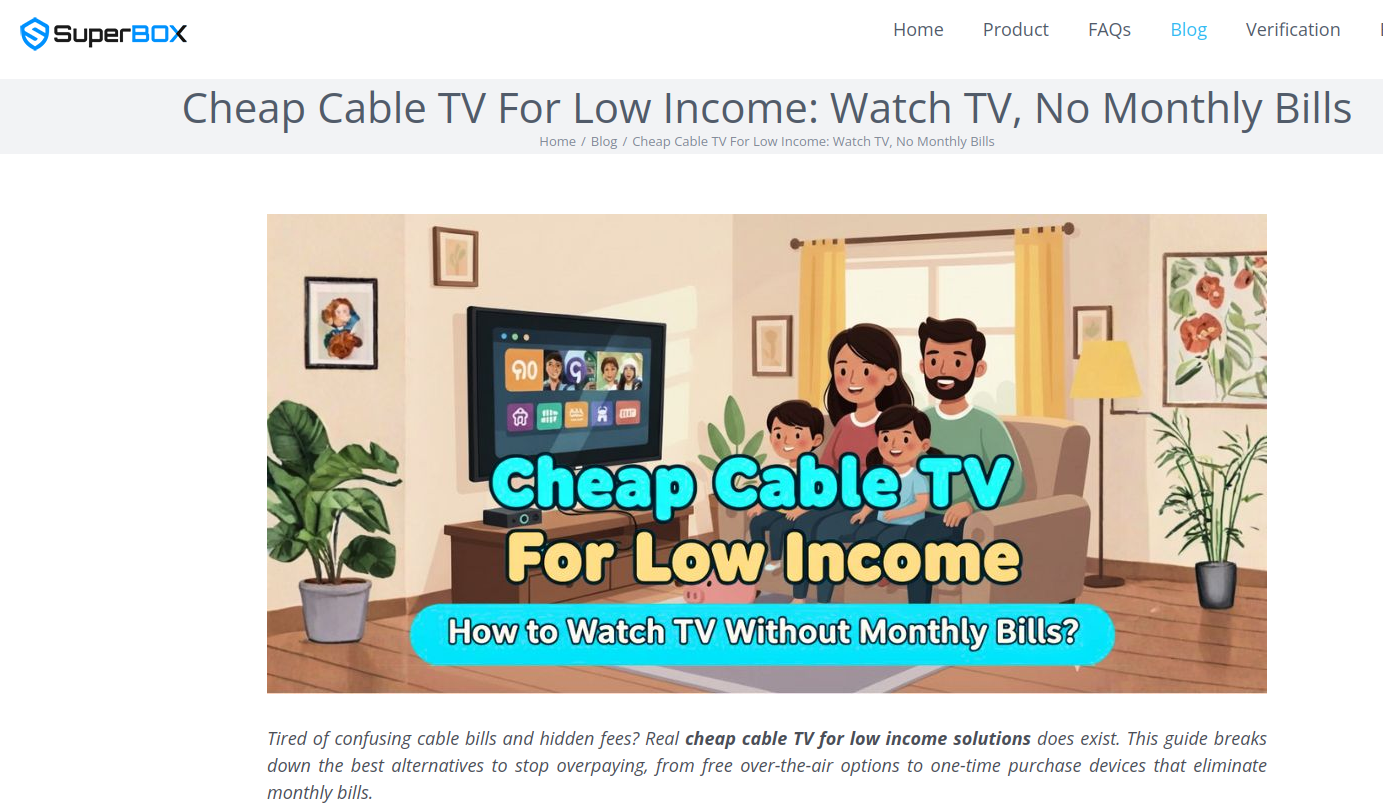
The #1 and #3 positions in this chart are Aisuru botnet controllers with their full domain names redacted. Source: radar.cloudflare.com.
Aisuru is a rapidly growing botnet comprising hundreds of thousands of hacked Internet of Things (IoT) devices, such as poorly secured Internet routers and security cameras. The botnet has increased in size and firepower significantly since its debut in 2024, demonstrating the ability to launch record distributed denial-of-service (DDoS) attacks nearing 30 terabits of data per second.
Until recently, Aisuru’s malicious code instructed all infected systems to use DNS servers from Google — specifically, the servers at 8.8.8.8. But in early October, Aisuru switched to invoking Cloudflare’s main DNS server — 1.1.1.1 — and over the past week domains used by Aisuru to control infected systems started populating Cloudflare’s top domain rankings.
As screenshots of Aisuru domains claiming two of the Top 10 positions ping-ponged across social media, many feared this was yet another sign that an already untamable botnet was running completely amok. One Aisuru botnet domain that sat prominently for days at #1 on the list was someone’s street address in Massachusetts followed by “.com”. Other Aisuru domains mimicked those belonging to major cloud providers.
Cloudflare tried to address these security, brand confusion and privacy concerns by partially redacting the malicious domains, and adding a warning at the top of its rankings:
“Note that the top 100 domains and trending domains lists include domains with organic activity as well as domains with emerging malicious behavior.”
Cloudflare CEO Matthew Prince told KrebsOnSecurity the company’s domain ranking system is fairly simplistic, and that it merely measures the volume of DNS queries to 1.1.1.1.
“The attacker is just generating a ton of requests, maybe to influence the ranking but also to attack our DNS service,” Prince said, adding that Cloudflare has heard reports of other large public DNS services seeing similar uptick in attacks. “We’re fixing the ranking to make it smarter. And, in the meantime, redacting any sites we classify as malware.”
Renee Burton, vice president of threat intel at the DNS security firm Infoblox, said many people erroneously assumed that the skewed Cloudflare domain rankings meant there were more bot-infected devices than there were regular devices querying sites like Google and Apple and Microsoft.
“Cloudflare’s documentation is clear — they know that when it comes to ranking domains you have to make choices on how to normalize things,” Burton wrote on LinkedIn. “There are many aspects that are simply out of your control. Why is it hard? Because reasons. TTL values, caching, prefetching, architecture, load balancing. Things that have shared control between the domain owner and everything in between.”
Alex Greenland is CEO of the anti-phishing and security firm Epi. Greenland said he understands the technical reason why Aisuru botnet domains are showing up in Cloudflare’s rankings (those rankings are based on DNS query volume, not actual web visits). But he said they’re still not meant to be there.
“It’s a failure on Cloudflare’s part, and reveals a compromise of the trust and integrity of their rankings,” he said.
Greenland said Cloudflare planned for its Domain Rankings to list the most popular domains as used by human users, and it was never meant to be a raw calculation of query frequency or traffic volume going through their 1.1.1.1 DNS resolver.
“They spelled out how their popularity algorithm is designed to reflect real human use and exclude automated traffic (they said they’re good at this),” Greenland wrote on LinkedIn. “So something has evidently gone wrong internally. We should have two rankings: one representing trust and real human use, and another derived from raw DNS volume.”
Why might it be a good idea to wholly separate malicious domains from the list? Greenland notes that Cloudflare Domain Rankings see widespread use for trust and safety determination, by browsers, DNS resolvers, safe browsing APIs and things like TRANCO.
“TRANCO is a respected open source list of the top million domains, and Cloudflare Radar is one of their five data providers,” he continued. “So there can be serious knock-on effects when a malicious domain features in Cloudflare’s top 10/100/1000/million. To many people and systems, the top 10 and 100 are naively considered safe and trusted, even though algorithmically-defined top-N lists will always be somewhat crude.”
Over this past week, Cloudflare started redacting portions of the malicious Aisuru domains from its Top Domains list, leaving only their domain suffix visible. Sometime in the past 24 hours, Cloudflare appears to have begun hiding the malicious Aisuru domains entirely from the web version of that list. However, downloading a spreadsheet of the current Top 200 domains from Cloudflare Radar shows an Aisuru domain still at the very top.
According to Cloudflare’s website, the majority of DNS queries to the top Aisuru domains — nearly 52 percent — originated from the United States. This tracks with my reporting from early October, which found Aisuru was drawing most of its firepower from IoT devices hosted on U.S. Internet providers like AT&T, Comcast and Verizon.
Experts tracking Aisuru say the botnet relies on well more than a hundred control servers, and that for the moment at least most of those domains are registered in the .su top-level domain (TLD). Dot-su is the TLD assigned to the former Soviet Union (.su’s Wikipedia page says the TLD was created just 15 months before the fall of the Berlin wall).
A Cloudflare blog post from October 27 found that .su had the highest “DNS magnitude” of any TLD, referring to a metric estimating the popularity of a TLD based on the number of unique networks querying Cloudflare’s 1.1.1.1 resolver. The report concluded that the top .su hostnames were associated with a popular online world-building game, and that more than half of the queries for that TLD came from the United States, Brazil and Germany [it’s worth noting that servers for the world-building game Minecraft were some of Aisuru’s most frequent targets].
A simple and crude way to detect Aisuru bot activity on a network may be to set an alert on any systems attempting to contact domains ending in .su. This TLD is frequently abused for cybercrime and by cybercrime forums and services, and blocking access to it entirely is unlikely to raise any legitimate complaints.
How to Crack Passwords in the Cloud with GPU Acceleration (Kali 2017)
Carrie Roberts* // How does password cracking in the cloud compare to down here on earth? Maybe not as heavenly as imagined. I saw this on the web and got […]
The post How to Crack Passwords in the Cloud with GPU Acceleration (Kali 2017) appeared first on Black Hills Information Security, Inc..