MacOS 26.4 Adds Warnings For ClickFix Attacks to Its Terminal App
Read more of this story at Slashdot.
Read more of this story at Slashdot.
Read more of this story at Slashdot.
Read more of this story at Slashdot.
Apple disclosed an exceptionally high number of vulnerabilities in core services and components used across its most popular devices, as the tech giant addressed 105 vulnerabilities in MacOS 26.1 and 56 vulnerabilities with the release of iOS 26.1 and iPadOS 26.1.
The company’s latest security update includes some flaws that affect software spanning iPhones, Macs and iPads. Apple did not report active exploitation of any vulnerabilities it patched Monday.
Apple’s vulnerability disclosure strategy remains a challenge and point of contention for outside threat researchers who are trying to gauge which vulnerabilities to prioritize for further review. The company doesn’t follow the Common Vulnerability Scoring System and provides minimal details about the potential impact and description of each vulnerability.
“As always, I get frustrated when reading Apple updates as they don’t provide any severity rating,” Dustin Childs, head of threat awareness at Trend Micro’s Zero Day Initiative, told CyberScoop. “I understand not wanting to use CVSS, but if they would at least call out the critical and high-severity bugs, it would be greatly appreciated.”
Apple customers have experienced a respite from zero-day vulnerabilities, following a steady pace of emergency software updates earlier this year. The company has addressed five actively exploited zero-days this year, including defects previously disclosed in January, February, March, April and August.
The Cybersecurity and Infrastructure Security Agency has added eight Apple defects to its known exploited vulnerabilities catalog this year.
Childs said he was particularly surprised by the size of Apple’s security release and the number of fixes for WebKit, the open-source web browser engine used across the vendor’s products.
Seven of the WebKit defects described the potential of an unexpected process crash from the processing of maliciously crafted web content.
“I was also disappointed to read some of the descriptions of CVEs played down or didn’t specifically call out the chance for arbitrary code execution,” Childs said.
Apple also patched 21 defects with the release of Safari 26.1, 43 vulnerabilities in visionOS 26.1, 32 bugs in watchOS 26.1 and two defects in Xcode 26.1.
More information about the vulnerabilities and latest software versions are available on Apple’s security release site.
The post Apple addresses more than 100 vulnerabilities in security updates for iPhones, Macs and iPads appeared first on CyberScoop.
Cybercriminals are abusing a widespread lack of authentication in the customer service platform Zendesk to flood targeted email inboxes with menacing messages that come from hundreds of Zendesk corporate customers simultaneously.
Zendesk is an automated help desk service designed to make it simple for people to contact companies for customer support issues. Earlier this week, KrebsOnSecurity started receiving thousands of ticket creation notification messages through Zendesk in rapid succession, each bearing the name of different Zendesk customers, such as CapCom, CompTIA, Discord, GMAC, NordVPN, The Washington Post, and Tinder.
The abusive missives sent via Zendesk’s platform can include any subject line chosen by the abusers. In my case, the messages variously warned about a supposed law enforcement investigation involving KrebsOnSecurity.com, or else contained personal insults.
Moreover, the automated messages that are sent out from this type of abuse all come from customer domain names — not from Zendesk. In the example below, replying to any of the junk customer support responses from The Washington Post’s Zendesk installation shows the reply-to address is help@washpost.com.
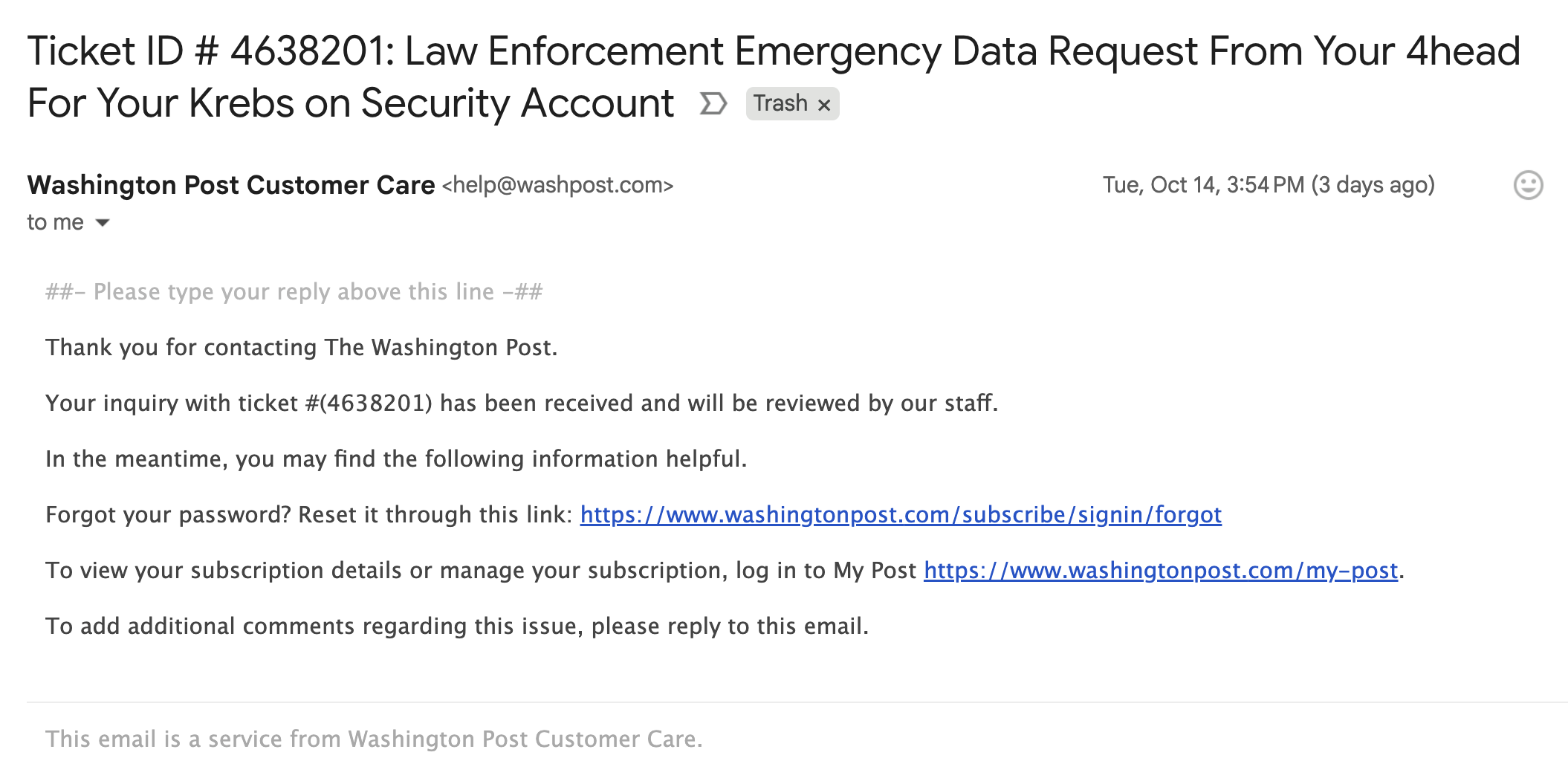
One of dozens of messages sent to me this week by The Washington Post.
Notified about the mass abuse of their platform, Zendesk said the emails were ticket creation notifications from customer accounts that configured their Zendesk instance to allow anyone to submit support requests — including anonymous users.
“These types of support tickets can be part of a customer’s workflow, where a prior verification is not required to allow them to engage and make use of the Support capabilities,” said Carolyn Camoens, communications director at Zendesk. “Although we recommend our customers to permit only verified users to submit tickets, some Zendesk customers prefer to use an anonymous environment to allow for tickets to be created due to various business reasons.”
Camoens said requests that can be submitted in an anonymous manner can also make use of an email address of the submitter’s choice.
“However, this method can also be used for spam requests to be created on behalf of third party email addresses,” Camoens said. “If an account has enabled the auto-responder trigger based on ticket creation, then this allows for the ticket notification email to be sent from our customer’s accounts to these third parties. The notification will also include the Subject added by the creator of these tickets.”
Zendesk claims it uses rate limits to prevent a high volume of requests from being created at once, but those limits did not stop Zendesk customers from flooding my inbox with thousands of messages in just a few hours.
“We recognize that our systems were leveraged against you in a distributed, many-against-one manner,” Camoens said. “We are actively investigating additional preventive measures. We are also advising customers experiencing this type of activity to follow our general security best practices and configure an authenticated ticket creation workflow.”
In all of the cases above, the messaging abuse would not have been possible if Zendesk customers validated support request email addresses prior to sending responses. Failing to do so may make it easier for Zendesk clients to handle customer support requests, but it also allows ne’er-do-wells to sully the sender’s brand in service of disruptive and malicious email floods.
David Fletcher // Recently we were involved in an engagement where we expected to see a large number of Macs in the target environment. As an element of the engagement […]
The post How to Phish for Geniuses appeared first on Black Hills Information Security, Inc..