The AI era demands a different kind of CISO
Many security leaders are still operating with frameworks built for a different era. For years, success was measured by fixed checkpoints, such as passing audits, closing vulnerabilities, and maintaining compliance. Those markers still have value, but they were designed for a threat landscape that moved in predictable, linear ways.
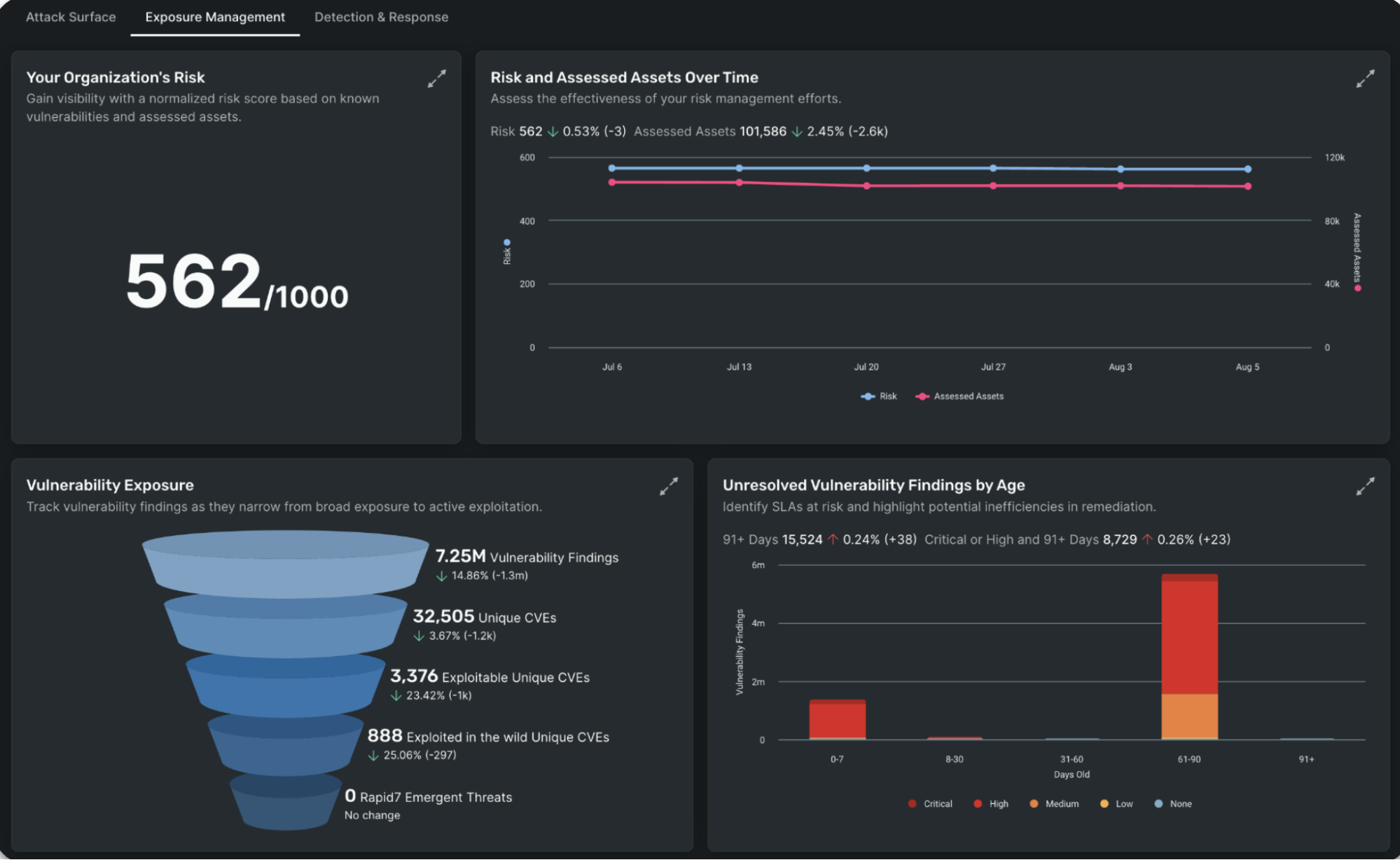
Today, that landscape is shifting in real time. AI is accelerating how attackers can identify and exploit weaknesses, while cloud environments and autonomous systems are constantly changing the terrain. The result is a gap between how risk is measured and how it actually unfolds, where static signals can’t keep up with dynamic threats.
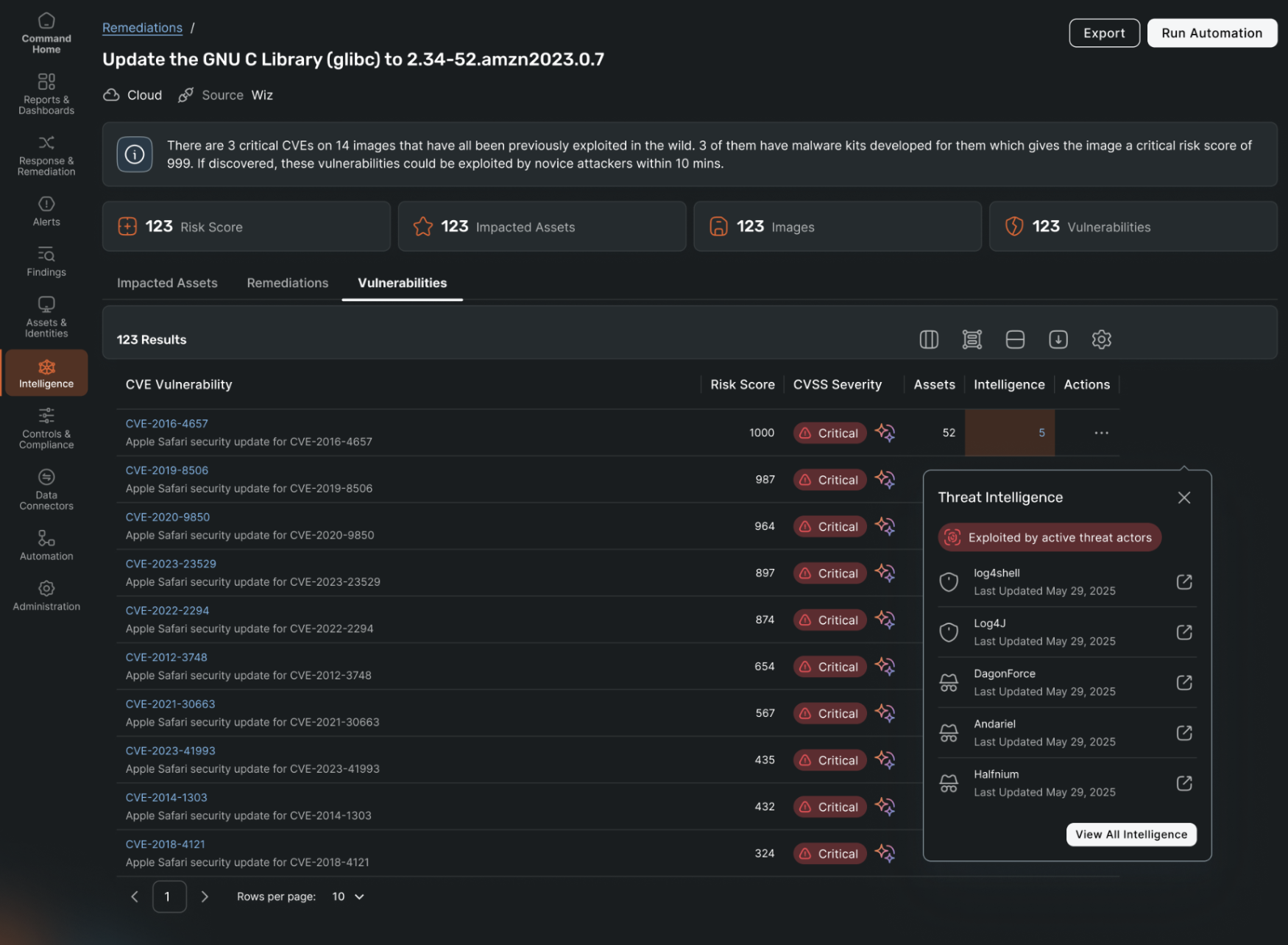
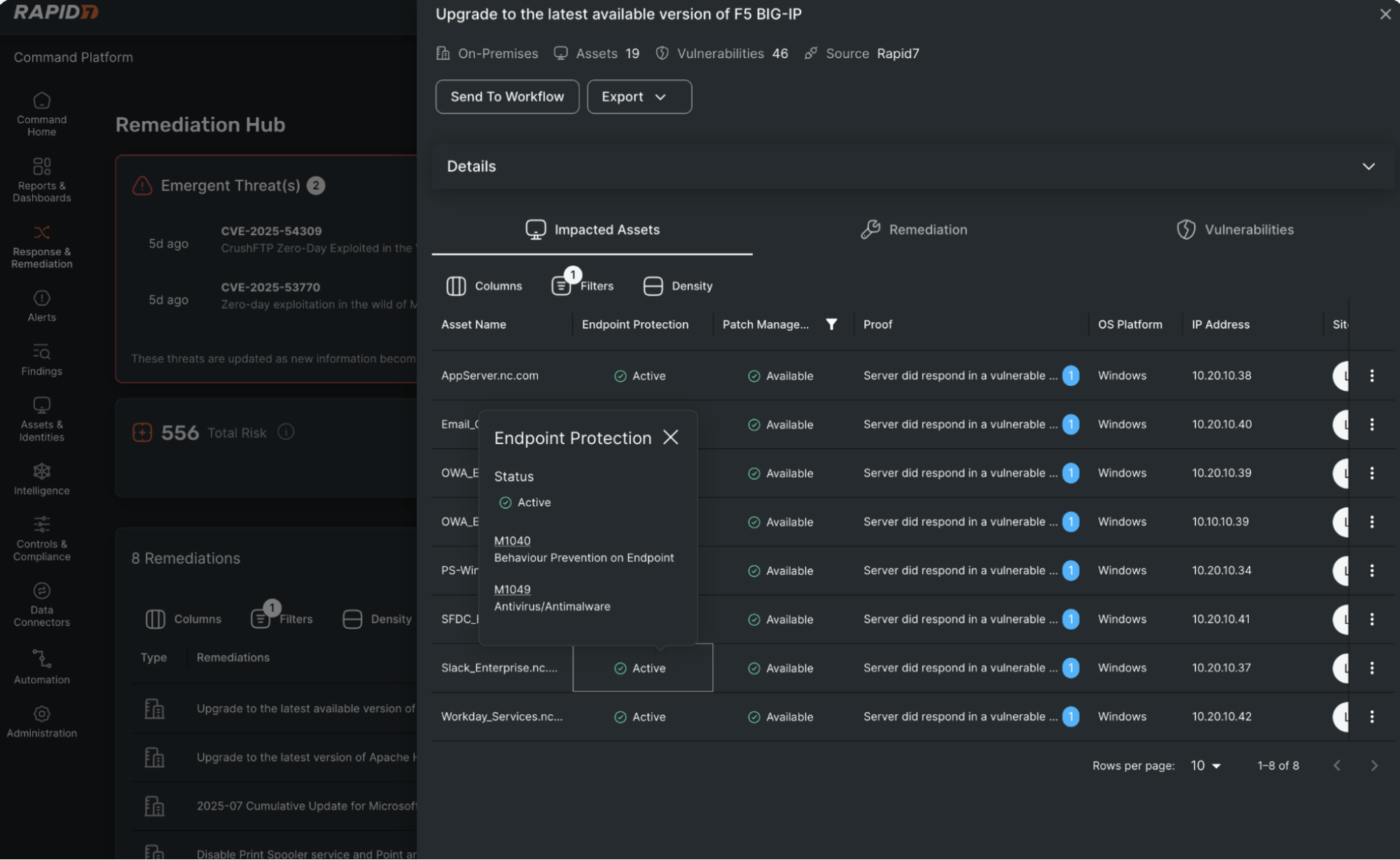
CISOs are under pressure from two directions: risk is growing, and the tools meant to measure it are struggling to keep up. Traditional indicators often reflect yesterday’s threat landscape, leaving security leaders with an incomplete picture of where they actually stand.
The Mythos signal
Recent reports about Anthropic’s Claude Mythos Preview, described as so effective at vulnerability discovery that access has been restricted, offer a clear signal of where cybersecurity is headed. AI models like this one demonstrate that the speed and scale of exploitation have fundamentally changed. What once took skilled attackers days or weeks can now happen in minutes, and increasingly without human intervention.
That shift matters because attacker capabilities are accelerating faster than most organizations can measure them. The gap between how risk unfolds and how security teams track it is widening. A “passed” audit tells you where you’ve been, not where you are. A posture dashboard reflects a moment in time, not a continuously changing environment. And a pen test is a snapshot, in a world where conditions evolve constantly.
Sharpening the conversation this quarter
If your conversations haven’t evolved to match this new reality, your organization has a significant blind spot. Here are five questions CISOs should be using to turn the current shift into action:
What can we see at runtime without waiting for a report?
Configuration tools tell you what should be true. Runtime visibility tells you what is true right now. (Follow up: If an attacker starts moving laterally in our cloud environment today, how fast do we know, in minutes or days?)
Do we have a complete inventory of identities, including non-human?
Business environments are full of identities beyond employees. Vendors, contractors, service accounts, API keys, automations, machine identities, and cloud principals sprawl across systems. Attackers love that sprawl because stealing credentials is often easier than writing malware.
(Follow up: How many human and non-human identities do we have, and which ones can access sensitive data or modify critical infrastructure?)
Where are we over-permissioned, and how quickly can we reduce it?
Over-permissioned accounts act like master keys: convenient until they’re compromised. Least privilege must be measurable, not aspirational. (Follow up: Can you show me the highest-risk access paths and what we can remove or tighten in 30 days?)
Are we using AI to reduce noise and speed decisions or just adding another screen?
Many teams are drowning in alerts. AI can help by adding context (connecting a risky identity + vulnerable workload + exposed secret) so responders can act quickly, instead of chasing disconnected warnings. (Follow up: What’s our alert volume, what percentage is actionable, and what’s improved response time?)
Can you walk me through a realistic incident end to end, with decision points?
Prevention matters, but resilience is what separates organizations when something gets through. Incidents are inevitable. What matters is detection speed, containment, recovery, and communications. (Follow up: Pick a scenario — credential theft, ransomware, vendor compromise — What happens here, who decides what, and when does executive leadership need to know? What do customers need to know?)
What to do with the answers
If these questions surface gaps, the path forward is usually practical. Start by prioritizing runtime visibility on systems that support critical services and sensitive resident data. Treat identity like infrastructure — inventory it, right-size permissions, and monitor continuously. Shift measurement toward outcomes like time to detect, contain, and restore, rather than activity metrics like tickets closed or controls checked. And rehearse the hard day with both technical teams and leadership, including communications.
In an era where threats move at AI speed, the advantage belongs to teams that can see clearly and act immediately. The defining question now is how quickly you can identify a risk, understand its impact, and respond before it escalates.
Rinki Sethi is the chief security & strategy officer at Upwind Security, holding over two decades of cybersecurity leadership experience from roles at Twitter, Rubrik, BILL, Palo Alto Networks, IBM, and eBay. She is a founding partner at Lockstep Ventures, serves on the boards of ForgeRock and Vaultree, and is widely recognized for her contributions to the cybersecurity community, including developing the first national cybersecurity curriculum for the Girl Scouts of USA.
The post The AI era demands a different kind of CISO appeared first on CyberScoop.