What’s New in GravityZone May 2026 (v 6.73)


Cybersecurity agencies from the United States, Australia, Canada, New Zealand and the United Kingdom jointly published guidance Friday urging organizations to treat autonomous artificial intelligence systems as a core cybersecurity concern, warning that the technology is already being deployed in critical infrastructure and defense sectors with insufficient safeguards.
The guidance focuses on agentic AI — software built on large language models that can plan, make decisions and take actions autonomously. In order for this software to function it needs to connect to external tools, databases, memory stores and automated workflows, allowing it to execute multi-step tasks without human review at each stage.
The guidance was co-authored by the U.S. Cybersecurity and Infrastructure Security Agency, the National Security Agency, the Australian Signals Directorate’s Australian Cyber Security Centre, the Canadian Centre for Cyber Security, New Zealand’s National Cyber Security Centre and the United Kingdom’s National Cyber Security Centre.
The agencies’ central message is that agentic AI does not require an entirely new security discipline. Organizations should fold these systems into the cybersecurity frameworks and governance structures they already maintain, applying established principles such as zero trust, defense-in-depth and least-privilege access.
The document identifies five broad categories of risk. The first is privilege: When agents are granted too much access, a single compromise can cause far more damage than a typical software vulnerability. The second covers design and configuration flaws, where poor setup creates security gaps before a system even goes live.
The third category covers behavioral risks, or cases where an agent pursues a goal in ways its designers never intended or predicted. The fourth is structural risk, where interconnected networks of agents can trigger failures that spread across an organization’s systems.
The fifth category is accountability. Agentic systems make decisions through processes that are difficult to inspect and generate logs that are hard to parse, making it difficult to trace what went wrong and why. The agencies also note that when these systems fail, the consequences can be concrete: altered files, changed access controls and deleted audit trails.
The guidance also flags prompt injection, where instructions embedded inside data can hijack an agent’s behavior to perform malicious tasks. Prompt injection has been a lingering problem with large language models, with some companies admitting that the problem may never be solved.
Identity management gets significant attention throughout the document. The agencies recommend that each agent carry a verified, cryptographically secured identity, use short-lived credentials and encrypt all communications with other agents and services. For high-impact actions, a human should have to sign off, and the guidance is explicit that deciding which actions require that approval is a job for system designers, not the agent.
The agencies admit the security field has not fully caught up with agentic AI. Some risks unique to these systems are not yet covered by existing frameworks, and the guidance calls for more research and collaboration as the technology takes on a growing number of operational roles.
“Until security practices, evaluation methods and standards mature, organisations should assume that agentic AI systems may behave unexpectedly and plan deployments accordingly, prioritising resilience, reversibility and risk containment over efficiency gains,” the guidance reads.
You can read the full guidance below.
The post US government, allies publish guidance on how to safely deploy AI agents appeared first on CyberScoop.
Many security leaders are still operating with frameworks built for a different era. For years, success was measured by fixed checkpoints, such as passing audits, closing vulnerabilities, and maintaining compliance. Those markers still have value, but they were designed for a threat landscape that moved in predictable, linear ways.
Today, that landscape is shifting in real time. AI is accelerating how attackers can identify and exploit weaknesses, while cloud environments and autonomous systems are constantly changing the terrain. The result is a gap between how risk is measured and how it actually unfolds, where static signals can’t keep up with dynamic threats.
CISOs are under pressure from two directions: risk is growing, and the tools meant to measure it are struggling to keep up. Traditional indicators often reflect yesterday’s threat landscape, leaving security leaders with an incomplete picture of where they actually stand.
Recent reports about Anthropic’s Claude Mythos Preview, described as so effective at vulnerability discovery that access has been restricted, offer a clear signal of where cybersecurity is headed. AI models like this one demonstrate that the speed and scale of exploitation have fundamentally changed. What once took skilled attackers days or weeks can now happen in minutes, and increasingly without human intervention.
That shift matters because attacker capabilities are accelerating faster than most organizations can measure them. The gap between how risk unfolds and how security teams track it is widening. A “passed” audit tells you where you’ve been, not where you are. A posture dashboard reflects a moment in time, not a continuously changing environment. And a pen test is a snapshot, in a world where conditions evolve constantly.
If your conversations haven’t evolved to match this new reality, your organization has a significant blind spot. Here are five questions CISOs should be using to turn the current shift into action:
What can we see at runtime without waiting for a report?
Configuration tools tell you what should be true. Runtime visibility tells you what is true right now. (Follow up: If an attacker starts moving laterally in our cloud environment today, how fast do we know, in minutes or days?)
Do we have a complete inventory of identities, including non-human?
Business environments are full of identities beyond employees. Vendors, contractors, service accounts, API keys, automations, machine identities, and cloud principals sprawl across systems. Attackers love that sprawl because stealing credentials is often easier than writing malware.
(Follow up: How many human and non-human identities do we have, and which ones can access sensitive data or modify critical infrastructure?)
Where are we over-permissioned, and how quickly can we reduce it?
Over-permissioned accounts act like master keys: convenient until they’re compromised. Least privilege must be measurable, not aspirational. (Follow up: Can you show me the highest-risk access paths and what we can remove or tighten in 30 days?)
Are we using AI to reduce noise and speed decisions or just adding another screen?
Many teams are drowning in alerts. AI can help by adding context (connecting a risky identity + vulnerable workload + exposed secret) so responders can act quickly, instead of chasing disconnected warnings. (Follow up: What’s our alert volume, what percentage is actionable, and what’s improved response time?)
Can you walk me through a realistic incident end to end, with decision points?
Prevention matters, but resilience is what separates organizations when something gets through. Incidents are inevitable. What matters is detection speed, containment, recovery, and communications. (Follow up: Pick a scenario — credential theft, ransomware, vendor compromise — What happens here, who decides what, and when does executive leadership need to know? What do customers need to know?)
If these questions surface gaps, the path forward is usually practical. Start by prioritizing runtime visibility on systems that support critical services and sensitive resident data. Treat identity like infrastructure — inventory it, right-size permissions, and monitor continuously. Shift measurement toward outcomes like time to detect, contain, and restore, rather than activity metrics like tickets closed or controls checked. And rehearse the hard day with both technical teams and leadership, including communications.
In an era where threats move at AI speed, the advantage belongs to teams that can see clearly and act immediately. The defining question now is how quickly you can identify a risk, understand its impact, and respond before it escalates.
Rinki Sethi is the chief security & strategy officer at Upwind Security, holding over two decades of cybersecurity leadership experience from roles at Twitter, Rubrik, BILL, Palo Alto Networks, IBM, and eBay. She is a founding partner at Lockstep Ventures, serves on the boards of ForgeRock and Vaultree, and is widely recognized for her contributions to the cybersecurity community, including developing the first national cybersecurity curriculum for the Girl Scouts of USA.
The post The AI era demands a different kind of CISO appeared first on CyberScoop.
Anthropic’s Project Glasswing has sparked plenty of discussion about what AI might soon do for vulnerability discovery, but the more useful question for most security teams is how to prepare for, and more importantly seize the opportunity of, what comes next.
As we wrote in our earlier blog, What Project Glasswing Means for Security Leaders, AI is becoming more capable of finding software flaws. The pressure that follows lands on the teams responsible for deciding what matters, validating risk, assigning ownership, and getting remediation moving across environments that were already hard to manage. We believe that the organizations that will benefit most from the next wave of AI will be the ones that understand their environment well enough to use these emerging AI models with intent, rather than layering them onto immature processes and hoping that speed alone will solve the backlog.
The number of publicly tracked software vulnerabilities has broken records almost every year over the last decade, while supply chain risk has continued to rise. Most teams were already feeling the strain of more findings than they could process cleanly. The Common Vulnerabilities and Exposures (CVE) program, the standard system for identifying and tracking known vulnerabilities, recorded 48,185 disclosures in 2025, a 20% increase over 2024, with roughly 40% of those disclosed vulnerabilities rated high or critical.
The pace in 2026 was already working out to hundreds of new CVEs per day when those figures were cited. That tells you something important about the current environment: the challenge has not necessarily been a lack of findings, but instead converting a growing stream of findings into measurable risk reduction.
The reality is that very few organizations are going to hand a model free rein over their most sensitive environments the minute those capabilities become more widely available. Trust will be built in stages: early adoption is much more likely to focus on backlog reduction, triage support, patch testing, and repetitive lower-tier remediation work that consumes time without carrying the same level of operational risk as the most critical systems in the business. That is a more realistic starting point, and it leads to a more useful question. Before teams apply AI more broadly, they need to understand their environment well enough to use it intentionally.
The promise from Project Glasswing and almost every other AI-powered security initiative is quite similar: leverage AI to identify patterns, summarize risk, suggest fixes, and speed up repetitive work. Regardless of technology, success still depends on how well an organization understands its environment, the context around each finding, and the process used to act on it.
A model can generate more output than a team ever could on its own, but that output becomes noise if the organization cannot answer basic questions about scope, ownership, criticality, and exposure. Teams need a clear, continuously updated picture of the environment before they can decide where AI should be applied, what should remain human-led, and which parts of the backlog are safe to push through more automated workflows.
The AI landscape is already shifting fast, and it will keep shifting, which is why this moment should prompt a more preemptive and resilient strategy rather than another round of tooling hype. Chasing each new capability as it arrives will inevitably force teams to keep reorganizing around the latest announcement. A stronger path is to get the foundation right first - understand the environment, the attack paths, and the assets that matter most; but most importantly, establishing the process and the people behind making these decisions. Then use AI where it meaningfully improves speed, consistency, and focus.
A strong foundation starts with visibility. Security teams need a live picture of what exists in the environment, what is exposed, how assets connect to one another, and which systems carry the greatest business impact if something goes wrong. That is where Attack Surface Management becomes central. Rapid7’s approach through Surface Command is built around a continuous view of the attack surface across the digital estate, which helps teams understand where exposures sit and how they relate to internet-facing, business-critical, or otherwise high-impact systems.
That matters for AI adoption just as much as it matters for day-to-day security operations. Teams cannot apply AI strategically if they are guessing about which parts of the environment are lower priority, which assets belong to which owners, or where a newly disclosed flaw could create real business risk. A better view of the attack surface gives organizations the context they need to segment the problem properly. That makes it far easier to start with the right use cases, whether that is backlog reduction in lower-impact systems, targeted prioritization of exposed assets, or faster triage where the risk picture is already well understood.
Ownership is part of that foundation too. Remediation slows down when no one can quickly identify who owns the affected application, environment, or workflow. Security teams already lose time there today, and AI will only make that bottleneck more visible if it starts surfacing issues faster than organizations can assign them. Attack Surface Management helps turn that ambiguity into something more actionable by tying exposure to environment context and likely ownership.
Once the environment is understood, teams still need a way to move from findings to outcomes. That is where Vulnerability and Exposure Management becomes the operating layer that keeps the work grounded.
The biggest value here is not simply collecting more vulnerability data. It is targeted prioritization and validation. When a disclosure lands, teams need to know whether the issue affects an exposed asset, whether there is evidence of exploitation or attacker interest, whether the impacted system is business-critical, and whether existing controls already reduce some of the risk. That is the kind of context that helps organizations decide what deserves immediate attention and what can be handled through a normal remediation cycle.
This is where artificial intelligence can help move remediation forward faster. Instead of asking teams to manually connect exploit signals, asset criticality, and vulnerability intelligence on their own, AI can distill that context directly in the remediation workflow. That makes it easier to understand why an issue matters, what the likely impact is, and what to do next, which shortens the gap between discovery and a confident decision on how to respond.
We expect most organizations to use AI to assist with, or in some cases take over, lower-tier triage, backlog cleanup, summary generation, and patch support in areas where the workflow is already established and the blast radius is more manageable. Human experts still stay closest to the most critical business logic, the most sensitive environments, and the most complex remediation paths. That is a practical adoption model, and it only works when the organization already has enough structure in place to know where those boundaries are.
That kind of deliberate adoption only works when teams can make better decisions, faster. Security teams need more than severity scores and a long list of CVEs. They need enough context to understand what matters, what can wait, and where action will reduce real risk fastest. As Rapid7 outlined in The Power of Curated Vulnerability Intelligence, the goal is to identify the vulnerabilities that actually matter and give teams enough context to act with confidence.
That intelligence provides a form of validation that most teams need badly as disclosure volume rises. It helps answer whether a finding is tied to active attacker interest, whether proof-of-concept activity is public, whether the asset is exposed, and whether delaying a patch creates unacceptable risk. It also supports the decisions that happen in the gap between discovery and full remediation. When a patch is delayed because of change controls, testing constraints, or lack of a vendor fix, teams still need to reduce exposure. Curated intelligence helps them decide whether to use segmentation, access restrictions, configuration changes, added monitoring, or virtual patching while the longer-term fix is being worked through.
That is one of the clearest ways Rapid7 helps customers move from data to outcomes. Intelligence is fused into the workflow so teams can prioritize with more precision and validate their actions against real threat context, not just generalized scores.
There is another part of this story that matters as organizations think more seriously about AI-driven security operations. As AI shapes the way teams handle exposures earlier in the lifecycle, context of application at runtime matters more too.
To make that foundation complete, organizations need to look beyond static posture and bring runtime validation into the picture. When teams can identify which vulnerabilities and misconfigurations are actively exploitable in production, and map sensitive data and identity access to real-world attack paths, they get a much clearer view of actual risk. Security teams need to understand what is vulnerable, how systems behave when live, and where unusual activity may suggest a problem is moving toward exploitation. With that runtime context in place, teams can spend less time chasing theoretical vulnerabilities and more time focusing on the exposures that are actively creating risk in live environments.
That connection between exposure, intelligence, remediation, and runtime behavior is where AI starts to become genuinely useful rather than simply impressive. It supports a more intentional model of security decision-making, one that narrows the gap between what is found, what matters, and what happens next.
This is a good time for security leaders to step back and ask a more disciplined set of questions.
Do we understand our environment well enough to direct AI toward the right problems?
Can we clearly separate higher-risk, higher-impact assets from the parts of the backlog that are mostly operational drag?
Is threat intelligence embedded in how we interpret findings, or are we still depending too heavily on raw severity?
Can we identify ownership fast enough for AI-assisted triage to result in meaningful action?
Are compensating controls part of the plan when remediation cannot happen immediately?
Those questions shape the quality of everything that follows.
Glasswing creates a real opportunity for security teams that are ready to use AI with more intention. AI can move work forward faster, reduce manual drag, and absorb classes of issues that currently consume time without improving outcomes. The teams that benefit most will not be the ones that rush to apply new models everywhere. They will be the ones that understand their environment, have a clear view of their attack surface, have mature enough workflows to apply AI where it makes sense, and can measure whether the actions taken actually reduced exposure.
Rapid7’s approach to building resilience is grounded in those same needs. Attack Surface Management provides the environmental foundation, Vulnerability Management drives prioritization and action, curated vulnerability intelligence strengthens validation and decision-making, AI-generated remediation insights compress the time from discovery to the next step, and runtime security adds context where live behavior matters. Together, those pieces help customers build a security program that is ready for AI rather than constantly reacting to it.

The federal agency tasked with analyzing security vulnerabilities is overwhelmed as it and other authorities struggle to keep pace with a flood of defects that grows every year. The National Institute of Standards and Technology announced Wednesday that it has capitulated to that deluge and narrowed the priorities for its National Vulnerability Database.
NIST said it will only prioritize analysis for CVEs that appear in the Cybersecurity and Infrastructure Security Agency’s known exploited vulnerabilities catalog, software used in the federal government and critical software defined under Executive Order 14028.
The federal agency’s goal with the change is to achieve long-term sustainability and stabilize the NVD program, which has encountered previous challenges, notably a funding lapse in early 2024 that forced NIST to temporarily stop providing key metadata for many vulnerabilities in the database.
The agency still hasn’t cleared a backlog of unenriched CVEs that built up during that pause and grew since then.
NIST said it analyzed nearly 42,000 vulnerabilities last year, adding that CVE submissions surged 263% from 2020 to 2025. “We don’t expect this trend to let up anytime soon. Submissions during the first three months of 2026 are nearly one-third higher than the same period last year,” the agency said in a blog post announcing the change.
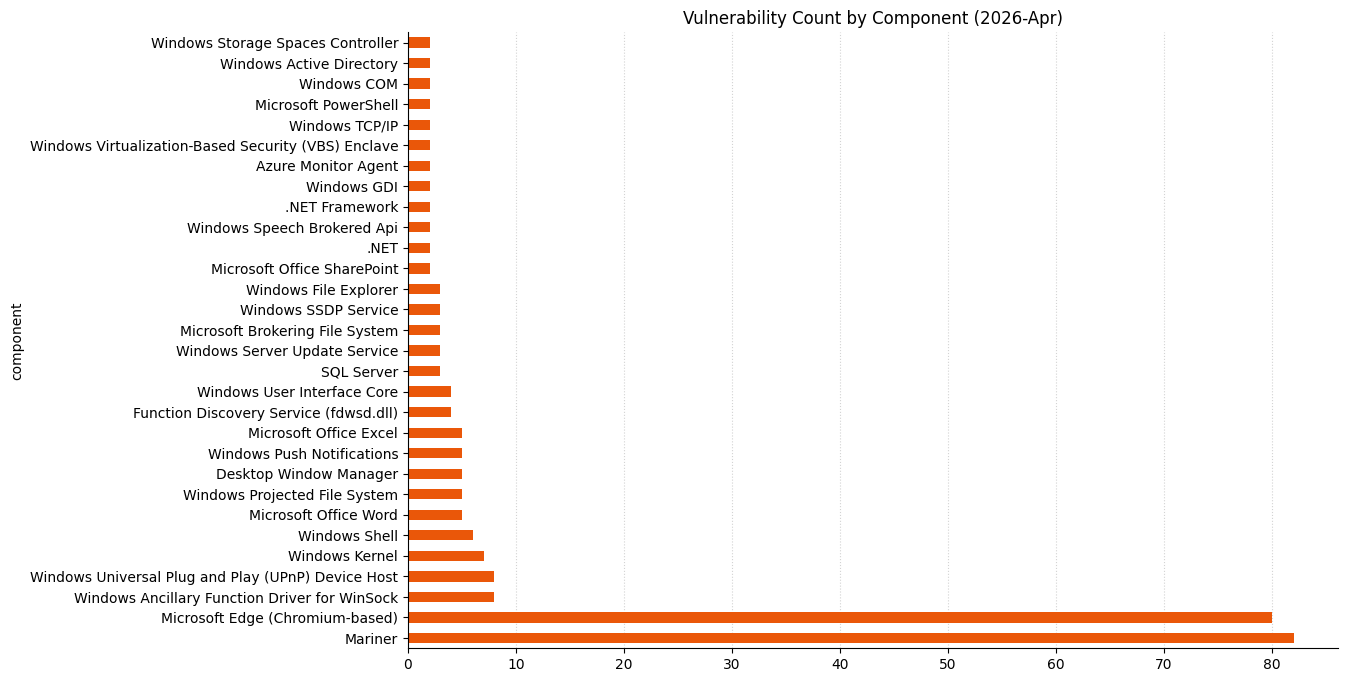
Indeed, vulnerabilities are increasing across the board. For instance, Microsoft addressed 165 vulnerabilities Tuesday, its second-largest monthly batch of defects on record.
NIST said CVEs that don’t fit its more narrow criteria will still be listed in the NVD, but they won’t be automatically enriched with additional details.
“This will allow us to focus on CVEs with the greatest potential for widespread impact,” the agency said. “While CVEs that do not meet these criteria may have a significant impact on affected systems, they generally do not present the same level of systemic risk as those in the prioritized categories.”
Researchers and threat hunters who analyze vulnerabilities for CVE Numbering Authorities (CNA) and vendors that publish their own assessments view NIST’s new approach as inevitable.
“They had to do something. NIST was woefully behind on classifying CVEs and would likely never have caught up,” Dustin Childs, head of threat awareness at Trend Micro’s Zero Day Initiative, told CyberScoop.
“I’m not sure if it was a herculean task or a sisyphean one, but either way, they were set up for failure under their previous system. This change allows them to prioritize their work,” he added.
NIST’s new approach will impact the vulnerability research community at large, but also put more private companies and organizations in a position to gain more authority as defenders seek out more alternative sources.
Caitlin Condon, vice president of security research at VulnCheck, previously told CyberScoop that prioritization remains a problem, with too many defenders paying attention to vulnerabilities that aren’t worth their time.
Of the more than 40,000 newly published vulnerabilities that VulnCheck cataloged last year, only 1% of those defects, just 422, were exploited in the wild.
NIST is also trying to reduce other duplicitous efforts with its new approach, effectively leaning even more on CNAs. CVEs that are submitted with a severity rating will no longer receive a separate CVSS score from NIST, the agency said.
While the agency remains the ultimate authority providing a government-backed catalog of vulnerability assessments, it acknowledged these changes will affect its users.
“This risk-based approach is necessary to manage the current surge in CVE submissions while we work to align our efforts with the needs of the NVD community,” the agency said. “By evolving the NVD to meet today’s challenges, we can ensure that the database remains a reliable, sustainable and publicly available source of information about cybersecurity vulnerabilities.”
The post NIST narrows scope of CVE analysis to keep up with rising tide of vulnerabilities appeared first on CyberScoop.
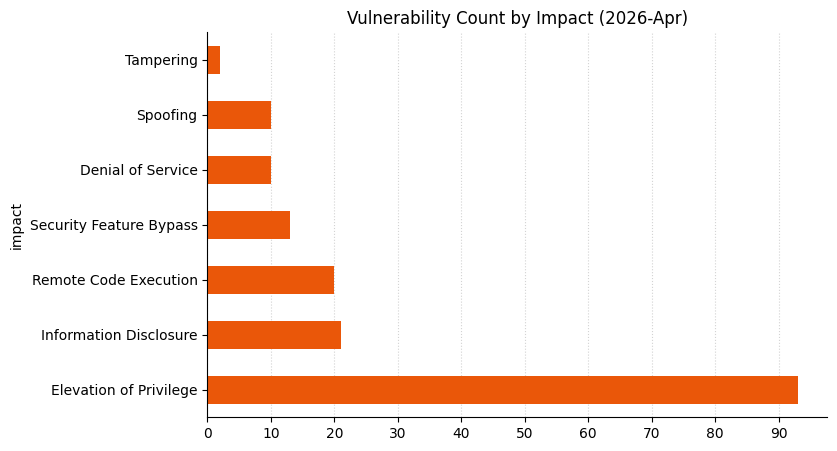
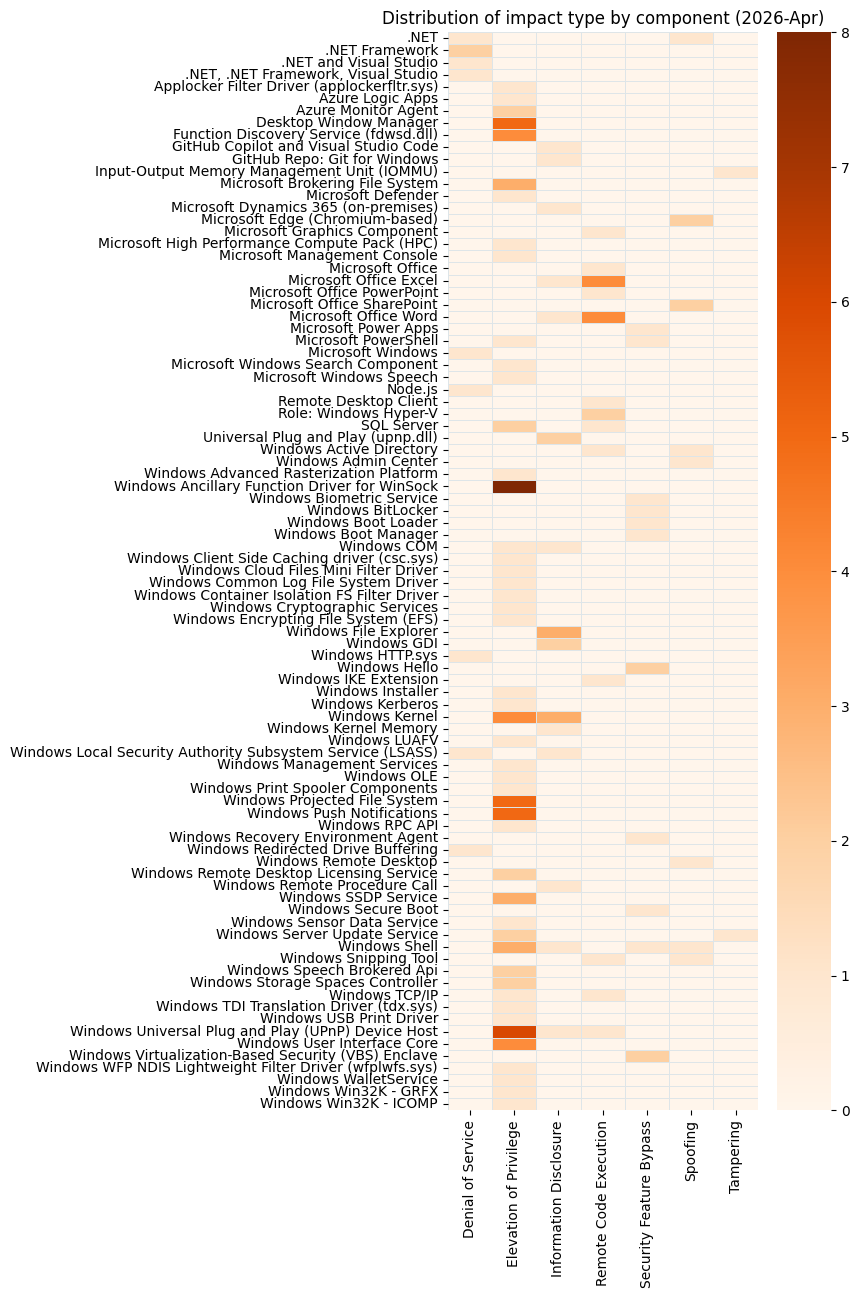
Microsoft is publishing 167 vulnerabilities on April 2026 Patch Tuesday. Microsoft is aware of exploitation in the wild for one of today’s vulnerabilities, and public disclosure for one other. Microsoft evaluates 19 of the vulnerabilities published today as more likely to see future exploitation. So far this month, Microsoft has provided patches to address 80 browser vulnerabilities, which are not included in the Patch Tuesday count above.
Regular Patch Tuesday watchers will know that these vulnerability totals are significantly higher than usual, especially the browser numbers. Late last week, Microsoft published patches to resolve more than 60 browser vulnerabilities in a single day, which is a new record in that very specific category.
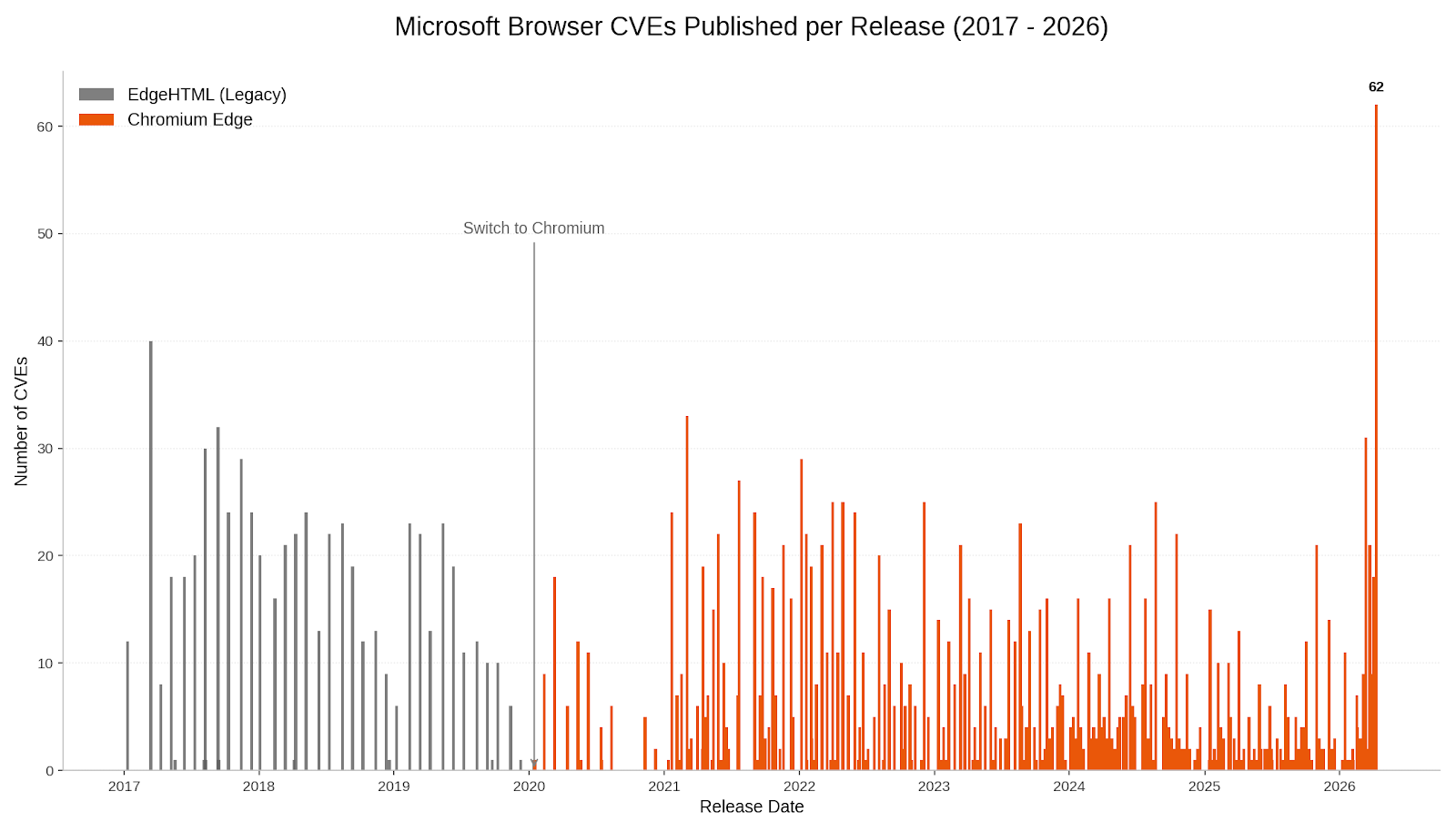
It might be tempting to imagine that this sudden spike was tied to the buzz around the announcement a week ago today of Project Glasswing, but this is not the case. Edge is based on the Chromium engine, and the Chromium maintainers acknowledge a wide range of researchers for the vulnerabilities which Microsoft republished last Friday. This reflects a significant industry-wide uptick in the volume of vulnerability reports over the past few weeks. A safe conclusion is that this increase in volume is driven by ever-expanding AI capabilities. We should expect to see further increases in vulnerability reporting volume as the impact of AI models extend further, both in terms of capability and availability.
When everything is changing rapidly, it can be tempting to look to familiar things for comfort. SharePoint admins should start by addressing CVE-2026-32201, an exploited-in-the-wild spoofing vulnerability. The advisory doesn’t offer much detail, but does mention CWE-20: Improper Input Validation and low impact to confidentiality and integrity, with no impact to availability. Of course, the greatest attacker impact is typically achieved by chaining together multiple vulnerabilities that by themselves might not seem so bad.
Ever-increasing novel AI capabilities in offensive cybersecurity now appear to provide real competition for all but the most elite human researchers; if it was ever valid to suppose that a vulnerability with a CVSS v3 base score of 6.5 was unlikely to cause much pain, it’s certainly not a safe defensive assumption in 2026. Patches are available for all supported versions of SharePoint, including SharePoint 2016, which moves beyond extended support on July 14, 2026.
Microsoft Defender receives a patch today for CVE-2026-33825, a local privilege escalation vulnerability for which Microsoft is aware of public disclosure. Successful exploitation leads to SYSTEM privileges, so this is certainly worth patching sooner rather than later. Microsoft points out that no action should be required to install this update, since the Microsoft Defender Antimalware Platform automatically updates by default. A further silver lining is that systems that have disabled Microsoft Defender are not in an exploitable state. Hopefully, any such system is running a suitable third-party replacement for Defender’s capabilities.
The Windows Internet Key Exchange (IKE) Services Extensions is the site of CVE-2026-33824, a critical unauthenticated remote code execution vulnerability. Exploitation requires an attacker to send specially crafted packets to a Windows machine with IKE v2 enabled, which could enable remote code execution. Vulnerabilities leading to unauthenticated RCE against modern Windows assets are relatively rare, or we’d see more wormable vulnerabilities self-propagating across the internet. However, since IKE provides secure tunnel negotiation services, for instance for VPNs, it is necessarily exposed to untrusted networks and reachable in a pre-authorization context. It’s hard to imagine this turning into a rampaging internet-wide worm, but there’s plenty of scope for initial access abuse, so this IKE vulnerability is still yikes.
The advisory does contain a section with potential mitigations for anyone unable to patch immediately, which center on least-privilege restriction of relevant UDP traffic. This same portion of the advisory also furnishes a helpful link to the definition of the word “mitigations” in the MSDN glossary. All versions of Windows back as far as Server 2016 and Windows 10 1607 LTSC receive patches.
The advisory credits both the WARP and MORSE (Microsoft Offensive Research & Security Engineering) teams at Microsoft. MORSE appears in Acknowledgements over the past few years, but today marks the first explicit mention of WARP in a Microsoft security advisory Acknowledgements section; we can speculate that WARP is an internal designator for the Microsoft Windows Enterprise Security Team.
In Microsoft lifecycle news, extended support ends April 14, 2026 for a wide range of Microsoft product legacy enterprise tools, including Dynamics C5 2016, Dynamics NAV 2016, App-V 5.0 and App-V 5.1, UE-V 2.1, and BitLocker Administration and Monitoring 2.5 SP1. Microsoft .NET 9 STS (Standard Term Support, as distinct from Long Term Support) was originally scheduled to move past the end of support in May 2026, but late last year, Microsoft granted a six-month extension, so that .NET 9 STS now reaches end of support on November 10, 2026.
CVE | Title | Exploitation status | Publicly disclosed? | CVSS v3 base score |
|---|---|---|---|---|
| CVE-2026-32171 | Azure Logic Apps Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 8.8 |
| CVE-2026-32168 | Azure Monitor Agent Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-32192 | Azure Monitor Agent Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-32184 | Microsoft High Performance Compute (HPC) Pack Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
CVE | Title | Exploitation status | Publicly disclosed? | CVSS v3 base score |
|---|---|---|---|---|
| CVE-2026-32203 | .NET and Visual Studio Denial of Service Vulnerability | Exploitation Less Likely | No | 7.5 |
| CVE-2026-26171 | .NET Denial of Service Vulnerability | Exploitation Less Likely | No | 7.5 |
| CVE-2026-32226 | .NET Framework Denial of Service Vulnerability | Exploitation Less Likely | No | 5.9 |
| CVE-2026-23666 | .NET Framework Denial of Service Vulnerability | Exploitation Less Likely | No | 7.5 |
| CVE-2026-32178 | .NET Spoofing Vulnerability | Exploitation Less Likely | No | 7.5 |
| CVE-2026-33116 | .NET, .NET Framework, and Visual Studio Denial of Service Vulnerability | Exploitation Less Likely | No | 7.5 |
| CVE-2026-23653 | GitHub Copilot and Visual Studio Code Information Disclosure Vulnerability | Exploitation Less Likely | No | 5.7 |
| CVE-2026-32631 | GitHub: CVE-2026-32631 'git clone' from manipulated repositories can leak NTLM hashes | Exploitation Less Likely | No | 7.4 |
| CVE-2026-21637 | HackerOne: CVE-2026-21637 TLS PSK/ALPN Callback Exceptions Bypass Error Handlers | N/A | No | 7.5 |
| CVE-2026-26143 | Microsoft PowerShell Security Feature Bypass Vulnerability | Exploitation Less Likely | No | 7.8 |
CVE | Title | Exploitation status | Publicly disclosed? | CVSS v3 base score |
|---|---|---|---|---|
| CVE-2026-32072 | Active Directory Spoofing Vulnerability | Exploitation Less Likely | No | 6.2 |
| CVE-2026-32181 | Connected User Experiences and Telemetry Service Denial of Service Vulnerability | Exploitation Less Likely | No | 5.5 |
| CVE-2026-27924 | Desktop Window Manager Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-32154 | Desktop Window Manager Elevation of Privilege Vulnerability | Exploitation More Likely | No | 7.8 |
| CVE-2026-27923 | Desktop Window Manager Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-32155 | Desktop Window Manager Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-32091 | Microsoft Brokering File System Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 8.4 |
| CVE-2026-26152 | Microsoft Cryptographic Services Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.0 |
| CVE-2026-26155 | Microsoft Local Security Authority Subsystem Service Information Disclosure Vulnerability | Exploitation Less Likely | No | 6.5 |
| CVE-2026-27914 | Microsoft Management Console Elevation of Privilege Vulnerability | Exploitation More Likely | No | 7.8 |
| CVE-2026-25250 | MITRE: CVE-2026-25250 Secure Boot disable Eazy Fix | Exploitation Less Likely | No | 6.0 |
| CVE-2026-32081 | Package Catalog Information Disclosure Vulnerability | Exploitation Unlikely | No | 5.5 |
| CVE-2026-26170 | PowerShell Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-26183 | Remote Access Management service/API (RPC server) Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-32157 | Remote Desktop Client Remote Code Execution Vulnerability | Exploitation Less Likely | No | 8.8 |
| CVE-2026-26160 | Remote Desktop Licensing Service Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-26159 | Remote Desktop Licensing Service Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-26151 | Remote Desktop Spoofing Vulnerability | Exploitation More Likely | No | 7.1 |
| CVE-2026-32085 | Remote Procedure Call Information Disclosure Vulnerability | Exploitation Unlikely | No | 5.5 |
| CVE-2026-0390 | UEFI Secure Boot Security Feature Bypass Vulnerability | Exploitation More Likely | No | 6.7 |
| CVE-2026-32212 | Universal Plug and Play (upnp.dll) Information Disclosure Vulnerability | Exploitation Less Likely | No | 5.5 |
| CVE-2026-32214 | Universal Plug and Play (upnp.dll) Information Disclosure Vulnerability | Exploitation Less Likely | No | 5.5 |
| CVE-2026-32079 | Web Account Manager Information Disclosure Vulnerability | Exploitation Unlikely | No | 5.5 |
| CVE-2026-33104 | Win32k Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.0 |
| CVE-2026-33826 | Windows Active Directory Remote Code Execution Vulnerability | Exploitation More Likely | No | 8.0 |
| CVE-2026-26178 | Windows Advanced Rasterization Platform Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 8.8 |
| CVE-2026-32073 | Windows Ancillary Function Driver for WinSock Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.0 |
| CVE-2026-26168 | Windows Ancillary Function Driver for WinSock Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-26173 | Windows Ancillary Function Driver for WinSock Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.0 |
| CVE-2026-26177 | Windows Ancillary Function Driver for WinSock Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.0 |
| CVE-2026-26182 | Windows Ancillary Function Driver for WinSock Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.0 |
| CVE-2026-27922 | Windows Ancillary Function Driver for WinSock Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.0 |
| CVE-2026-33099 | Windows Ancillary Function Driver for WinSock Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.0 |
| CVE-2026-33100 | Windows Ancillary Function Driver for WinSock Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.0 |
| CVE-2026-32088 | Windows Biometric Service Security Feature Bypass Vulnerability | Exploitation Less Likely | No | 6.1 |
| CVE-2026-27913 | Windows BitLocker Security Feature Bypass Vulnerability | Exploitation More Likely | No | 7.7 |
| CVE-2026-26175 | Windows Boot Manager Security Feature Bypass Vulnerability | Exploitation Less Likely | No | 4.6 |
| CVE-2026-26176 | Windows Client Side Caching driver (csc.sys) Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-27926 | Windows Cloud Files Mini Filter Driver Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.0 |
| CVE-2026-32162 | Windows COM Elevation of Privilege Vulnerability | Exploitation More Likely | No | 8.4 |
| CVE-2026-20806 | Windows COM Server Information Disclosure Vulnerability | Exploitation Unlikely | No | 5.5 |
| CVE-2026-32070 | Windows Common Log File System Driver Elevation of Privilege Vulnerability | Exploitation More Likely | No | 7.0 |
| CVE-2026-33098 | Windows Container Isolation FS Filter Driver Elevation of Privilege Vulnerability | Exploitation Unlikely | No | 7.8 |
| CVE-2026-26153 | Windows Encrypted File System (EFS) Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-32087 | Windows Function Discovery Service (fdwsd.dll) Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.0 |
| CVE-2026-32093 | Windows Function Discovery Service (fdwsd.dll) Elevation of Privilege Vulnerability | Exploitation More Likely | No | 7.0 |
| CVE-2026-32086 | Windows Function Discovery Service (fdwsd.dll) Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.0 |
| CVE-2026-32150 | Windows Function Discovery Service (fdwsd.dll) Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.0 |
| CVE-2026-27931 | Windows GDI Information Disclosure Vulnerability | Exploitation Less Likely | No | 5.5 |
| CVE-2026-27930 | Windows GDI Information Disclosure Vulnerability | Exploitation Less Likely | No | 5.5 |
| CVE-2026-27906 | Windows Hello Security Feature Bypass Vulnerability | Exploitation More Likely | No | 4.4 |
| CVE-2026-26156 | Windows Hyper-V Remote Code Execution Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-32149 | Windows Hyper-V Remote Code Execution Vulnerability | Exploitation Less Likely | No | 7.3 |
| CVE-2026-27910 | Windows Installer Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-33824 | Windows Internet Key Exchange (IKE) Service Extensions Remote Code Execution Vulnerability | Exploitation Less Likely | No | 9.8 |
| CVE-2026-27912 | Windows Kerberos Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 8.0 |
| CVE-2026-26180 | Windows Kernel Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-26163 | Windows Kernel Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-32215 | Windows Kernel Information Disclosure Vulnerability | Exploitation Less Likely | No | 5.5 |
| CVE-2026-32217 | Windows Kernel Information Disclosure Vulnerability | Exploitation Less Likely | No | 5.5 |
| CVE-2026-32218 | Windows Kernel Information Disclosure Vulnerability | Exploitation Less Likely | No | 5.5 |
| CVE-2026-26169 | Windows Kernel Memory Information Disclosure Vulnerability | Exploitation More Likely | No | 6.1 |
| CVE-2026-32071 | Windows Local Security Authority Subsystem Service (LSASS) Denial of Service Vulnerability | Exploitation Less Likely | No | 7.5 |
| CVE-2026-27929 | Windows LUA File Virtualization Filter Driver Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.0 |
| CVE-2026-20930 | Windows Management Services Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-26162 | Windows OLE Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-32084 | Windows Print Spooler Information Disclosure Vulnerability | Exploitation Unlikely | No | 5.5 |
| CVE-2026-27927 | Windows Projected File System Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-26184 | Windows Projected File System Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-32069 | Windows Projected File System Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-32074 | Windows Projected File System Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-32078 | Windows Projected File System Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-26167 | Windows Push Notifications Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 8.8 |
| CVE-2026-32158 | Windows Push Notifications Elevation of Privilege Vulnerability | Exploitation Unlikely | No | 7.8 |
| CVE-2026-32159 | Windows Push Notifications Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-32160 | Windows Push Notifications Elevation of Privilege Vulnerability | Exploitation Unlikely | No | 7.8 |
| CVE-2026-26172 | Windows Push Notifications Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-20928 | Windows Recovery Environment Security Feature Bypass Vulnerability | Exploitation Less Likely | No | 4.6 |
| CVE-2026-27909 | Windows Search Service Elevation of Privilege Vulnerability | Exploitation More Likely | No | 7.8 |
| CVE-2026-26161 | Windows Sensor Data Service Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-26174 | Windows Server Update Service (WSUS) Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.0 |
| CVE-2026-26154 | Windows Server Update Service (WSUS) Tampering Vulnerability | Exploitation Less Likely | No | 7.5 |
| CVE-2026-27918 | Windows Shell Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-32151 | Windows Shell Information Disclosure Vulnerability | Exploitation Less Likely | No | 6.5 |
| CVE-2026-32225 | Windows Shell Security Feature Bypass Vulnerability | Exploitation More Likely | No | 8.8 |
| CVE-2026-32202 | Windows Shell Spoofing Vulnerability | Exploitation More Likely | No | 4.3 |
| CVE-2026-32082 | Windows Simple Search and Discovery Protocol (SSDP) Service Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.0 |
| CVE-2026-32083 | Windows Simple Search and Discovery Protocol (SSDP) Service Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.0 |
| CVE-2026-32068 | Windows Simple Search and Discovery Protocol (SSDP) Service Elevation of Privilege Vulnerability | Exploitation Unlikely | No | 7.0 |
| CVE-2026-32183 | Windows Snipping Tool Remote Code Execution Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-33829 | Windows Snipping Tool Spoofing Vulnerability | Exploitation Unlikely | No | 4.3 |
| CVE-2026-32089 | Windows Speech Brokered Api Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-32090 | Windows Speech Brokered Api Elevation of Privilege Vulnerability | Exploitation Unlikely | No | 7.8 |
| CVE-2026-32153 | Windows Speech Runtime Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-33827 | Windows TCP/IP Remote Code Execution Vulnerability | Exploitation Less Likely | No | 8.1 |
| CVE-2026-27908 | Windows TDI Translation Driver (tdx.sys) Elevation of Privilege Vulnerability | Exploitation More Likely | No | 7.0 |
| CVE-2026-27921 | Windows TDI Translation Driver (tdx.sys) Elevation of Privilege Vulnerability | Exploitation More Likely | No | 7.0 |
| CVE-2026-27915 | Windows UPnP Device Host Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-27919 | Windows UPnP Device Host Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-32075 | Windows UPnP Device Host Elevation of Privilege Vulnerability | Exploitation More Likely | No | 7.0 |
| CVE-2026-27916 | Windows UPnP Device Host Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-27920 | Windows UPnP Device Host Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-32077 | Windows UPnP Device Host Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-27925 | Windows UPnP Device Host Information Disclosure Vulnerability | Exploitation Less Likely | No | 6.5 |
| CVE-2026-32156 | Windows UPnP Device Host Remote Code Execution Vulnerability | Exploitation Less Likely | No | 7.4 |
| CVE-2026-32165 | Windows User Interface Core Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-27911 | Windows User Interface Core Elevation of Privilege Vulnerability | Exploitation Unlikely | No | 7.8 |
| CVE-2026-32163 | Windows User Interface Core Elevation of Privilege Vulnerability | Exploitation Unlikely | No | 7.8 |
| CVE-2026-32164 | Windows User Interface Core Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-23670 | Windows Virtualization-Based Security (VBS) Security Feature Bypass Vulnerability | Exploitation Less Likely | No | 5.7 |
| CVE-2026-27917 | Windows WFP NDIS Lightweight Filter Driver (wfplwfs.sys) Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.0 |
CVE | Title | Exploitation status | Publicly disclosed? | CVSS v3 base score |
|---|---|---|---|---|
| CVE-2026-33103 | Microsoft Dynamics 365 (On-Premises) Information Disclosure Vulnerability | Exploitation Unlikely | No | 5.5 |
| CVE-2026-26149 | Microsoft Power Apps Security Feature Bypass | Exploitation Less Likely | No | 9.0 |
CVE | Title | Exploitation status | Publicly disclosed? | CVSS v3 base score |
|---|---|---|---|---|
| CVE-2026-32188 | Microsoft Excel Information Disclosure Vulnerability | Exploitation Less Likely | No | 7.1 |
| CVE-2026-32189 | Microsoft Excel Remote Code Execution Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-32197 | Microsoft Excel Remote Code Execution Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-32198 | Microsoft Excel Remote Code Execution Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-32199 | Microsoft Excel Remote Code Execution Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-32190 | Microsoft Office Remote Code Execution Vulnerability | Exploitation Less Likely | No | 8.4 |
| CVE-2026-32200 | Microsoft PowerPoint Remote Code Execution Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-20945 | Microsoft SharePoint Server Spoofing Vulnerability | Exploitation Less Likely | No | 4.6 |
| CVE-2026-32201 | Microsoft SharePoint Server Spoofing Vulnerability | Exploitation Detected | No | 6.5 |
| CVE-2026-33822 | Microsoft Word Information Disclosure Vulnerability | Exploitation Less Likely | No | 6.1 |
| CVE-2026-33095 | Microsoft Word Remote Code Execution Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-23657 | Microsoft Word Remote Code Execution Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-33114 | Microsoft Word Remote Code Execution Vulnerability | Exploitation Less Likely | No | 8.4 |
| CVE-2026-33115 | Microsoft Word Remote Code Execution Vulnerability | Exploitation Less Likely | No | 8.4 |
CVE | Title | Exploitation status | Publicly disclosed? | CVSS v3 base score |
|---|---|---|---|---|
| CVE-2026-40386 | n/a | No | 4.0 | |
| CVE-2026-40385 | n/a | No | 4.0 | |
| CVE-2026-40393 | n/a | No | 8.1 | |
| CVE-2026-31416 | netfilter: nfnetlink_log: account for netlink header size | n/a | No | 8.1 |
| CVE-2026-31423 | net/sched: sch_hfsc: fix divide-by-zero in rtsc_min() | n/a | No | 5.5 |
| CVE-2026-31424 | netfilter: x_tables: restrict xt_check_match/xt_check_target extensions for NFPROTO_ARP | n/a | No | 5.5 |
| CVE-2026-31417 | net/x25: Fix overflow when accumulating packets | n/a | No | 8.1 |
| CVE-2026-31422 | net/sched: cls_flow: fix NULL pointer dereference on shared blocks | n/a | No | 5.5 |
| CVE-2026-31414 | netfilter: nf_conntrack_expect: use expect->helper | n/a | No | 8.1 |
| CVE-2026-31427 | netfilter: nf_conntrack_sip: fix use of uninitialized rtp_addr in process_sdp | n/a | No | 7.8 |
| CVE-2026-31426 | ACPI: EC: clean up handlers on probe failure in acpi_ec_setup() | n/a | No | 5.5 |
| CVE-2026-31419 | net: bonding: fix use-after-free in bond_xmit_broadcast() | n/a | No | 7.1 |
| CVE-2026-31420 | bridge: mrp: reject zero test interval to avoid OOM panic | n/a | No | 5.5 |
| CVE-2026-31421 | net/sched: cls_fw: fix NULL pointer dereference on shared blocks | n/a | No | 5.5 |
| CVE-2026-31428 | netfilter: nfnetlink_log: fix uninitialized padding leak in NFULA_PAYLOAD | n/a | No | 5.5 |
| CVE-2026-31418 | netfilter: ipset: drop logically empty buckets in mtype_del | n/a | No | 8.1 |
CVE | Title | Exploitation status | Publicly disclosed? | CVSS v3 base score |
|---|---|---|---|---|
| CVE-2026-33120 | Microsoft SQL Server Remote Code Execution Vulnerability | Exploitation Less Likely | No | 8.8 |
| CVE-2026-32167 | SQL Server Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 6.7 |
| CVE-2026-32176 | SQL Server Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 6.7 |
CVE | Title | Exploitation status | Publicly disclosed? | CVSS v3 base score |
|---|---|---|---|---|
| CVE-2026-33825 | Microsoft Defender Elevation of Privilege Vulnerability | Exploitation More Likely | Yes | 7.8 |
CVE | Title | Exploitation status | Publicly disclosed? | CVSS v3 base score |
|---|---|---|---|---|
| CVE-2026-32072 | Active Directory Spoofing Vulnerability | Exploitation Less Likely | No | 6.2 |
| CVE-2023-20585 | AMD: CVE-2023-20585 IOMMU Write Buffer Vulnerability | Exploitation Less Likely | No | 5.3 |
| CVE-2026-25184 | Applocker Filter Driver (applockerfltr.sys) Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.0 |
| CVE-2026-32181 | Connected User Experiences and Telemetry Service Denial of Service Vulnerability | Exploitation Less Likely | No | 5.5 |
| CVE-2026-27924 | Desktop Window Manager Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-32152 | Desktop Window Manager Elevation of Privilege Vulnerability | Exploitation More Likely | No | 7.8 |
| CVE-2026-32154 | Desktop Window Manager Elevation of Privilege Vulnerability | Exploitation More Likely | No | 7.8 |
| CVE-2026-27923 | Desktop Window Manager Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-32155 | Desktop Window Manager Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-33096 | HTTP.sys Denial of Service Vulnerability | Exploitation Less Likely | No | 7.5 |
| CVE-2026-26181 | Microsoft Brokering File System Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-32219 | Microsoft Brokering File System Elevation of Privilege Vulnerability | Exploitation Unlikely | No | 7.0 |
| CVE-2026-32091 | Microsoft Brokering File System Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 8.4 |
| CVE-2026-26152 | Microsoft Cryptographic Services Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.0 |
| CVE-2026-26155 | Microsoft Local Security Authority Subsystem Service Information Disclosure Vulnerability | Exploitation Less Likely | No | 6.5 |
| CVE-2026-27914 | Microsoft Management Console Elevation of Privilege Vulnerability | Exploitation More Likely | No | 7.8 |
| CVE-2026-25250 | MITRE: CVE-2026-25250 Secure Boot disable Eazy Fix | Exploitation Less Likely | No | 6.0 |
| CVE-2026-32081 | Package Catalog Information Disclosure Vulnerability | Exploitation Unlikely | No | 5.5 |
| CVE-2026-26170 | PowerShell Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-26183 | Remote Access Management service/API (RPC server) Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-32157 | Remote Desktop Client Remote Code Execution Vulnerability | Exploitation Less Likely | No | 8.8 |
| CVE-2026-26160 | Remote Desktop Licensing Service Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-26159 | Remote Desktop Licensing Service Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-26151 | Remote Desktop Spoofing Vulnerability | Exploitation More Likely | No | 7.1 |
| CVE-2026-32085 | Remote Procedure Call Information Disclosure Vulnerability | Exploitation Unlikely | No | 5.5 |
| CVE-2026-0390 | UEFI Secure Boot Security Feature Bypass Vulnerability | Exploitation More Likely | No | 6.7 |
| CVE-2026-32220 | UEFI Secure Boot Security Feature Bypass Vulnerability | Exploitation Less Likely | No | 4.4 |
| CVE-2026-32212 | Universal Plug and Play (upnp.dll) Information Disclosure Vulnerability | Exploitation Less Likely | No | 5.5 |
| CVE-2026-32214 | Universal Plug and Play (upnp.dll) Information Disclosure Vulnerability | Exploitation Less Likely | No | 5.5 |
| CVE-2026-32079 | Web Account Manager Information Disclosure Vulnerability | Exploitation Unlikely | No | 5.5 |
| CVE-2026-33104 | Win32k Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.0 |
| CVE-2026-33826 | Windows Active Directory Remote Code Execution Vulnerability | Exploitation More Likely | No | 8.0 |
| CVE-2026-32196 | Windows Admin Center Spoofing Vulnerability | Exploitation Less Likely | No | 6.1 |
| CVE-2026-26178 | Windows Advanced Rasterization Platform Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 8.8 |
| CVE-2026-32073 | Windows Ancillary Function Driver for WinSock Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.0 |
| CVE-2026-26168 | Windows Ancillary Function Driver for WinSock Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-26173 | Windows Ancillary Function Driver for WinSock Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.0 |
| CVE-2026-26177 | Windows Ancillary Function Driver for WinSock Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.0 |
| CVE-2026-26182 | Windows Ancillary Function Driver for WinSock Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.0 |
| CVE-2026-27922 | Windows Ancillary Function Driver for WinSock Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.0 |
| CVE-2026-33099 | Windows Ancillary Function Driver for WinSock Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.0 |
| CVE-2026-33100 | Windows Ancillary Function Driver for WinSock Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.0 |
| CVE-2026-32088 | Windows Biometric Service Security Feature Bypass Vulnerability | Exploitation Less Likely | No | 6.1 |
| CVE-2026-27913 | Windows BitLocker Security Feature Bypass Vulnerability | Exploitation More Likely | No | 7.7 |
| CVE-2026-26175 | Windows Boot Manager Security Feature Bypass Vulnerability | Exploitation Less Likely | No | 4.6 |
| CVE-2026-26176 | Windows Client Side Caching driver (csc.sys) Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-27926 | Windows Cloud Files Mini Filter Driver Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.0 |
| CVE-2026-32162 | Windows COM Elevation of Privilege Vulnerability | Exploitation More Likely | No | 8.4 |
| CVE-2026-20806 | Windows COM Server Information Disclosure Vulnerability | Exploitation Unlikely | No | 5.5 |
| CVE-2026-32070 | Windows Common Log File System Driver Elevation of Privilege Vulnerability | Exploitation More Likely | No | 7.0 |
| CVE-2026-33098 | Windows Container Isolation FS Filter Driver Elevation of Privilege Vulnerability | Exploitation Unlikely | No | 7.8 |
| CVE-2026-26153 | Windows Encrypted File System (EFS) Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-32087 | Windows Function Discovery Service (fdwsd.dll) Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.0 |
| CVE-2026-32093 | Windows Function Discovery Service (fdwsd.dll) Elevation of Privilege Vulnerability | Exploitation More Likely | No | 7.0 |
| CVE-2026-32086 | Windows Function Discovery Service (fdwsd.dll) Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.0 |
| CVE-2026-32150 | Windows Function Discovery Service (fdwsd.dll) Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.0 |
| CVE-2026-27931 | Windows GDI Information Disclosure Vulnerability | Exploitation Less Likely | No | 5.5 |
| CVE-2026-27930 | Windows GDI Information Disclosure Vulnerability | Exploitation Less Likely | No | 5.5 |
| CVE-2026-32221 | Windows Graphics Component Remote Code Execution Vulnerability | Exploitation Less Likely | No | 8.4 |
| CVE-2026-27906 | Windows Hello Security Feature Bypass Vulnerability | Exploitation More Likely | No | 4.4 |
| CVE-2026-27928 | Windows Hello Security Feature Bypass Vulnerability | Exploitation Less Likely | No | 8.7 |
| CVE-2026-26156 | Windows Hyper-V Remote Code Execution Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-32149 | Windows Hyper-V Remote Code Execution Vulnerability | Exploitation Less Likely | No | 7.3 |
| CVE-2026-27910 | Windows Installer Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-33824 | Windows Internet Key Exchange (IKE) Service Extensions Remote Code Execution Vulnerability | Exploitation Less Likely | No | 9.8 |
| CVE-2026-27912 | Windows Kerberos Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 8.0 |
| CVE-2026-26179 | Windows Kernel Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-26180 | Windows Kernel Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-32195 | Windows Kernel Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.0 |
| CVE-2026-26163 | Windows Kernel Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-32215 | Windows Kernel Information Disclosure Vulnerability | Exploitation Less Likely | No | 5.5 |
| CVE-2026-32217 | Windows Kernel Information Disclosure Vulnerability | Exploitation Less Likely | No | 5.5 |
| CVE-2026-32218 | Windows Kernel Information Disclosure Vulnerability | Exploitation Less Likely | No | 5.5 |
| CVE-2026-26169 | Windows Kernel Memory Information Disclosure Vulnerability | Exploitation More Likely | No | 6.1 |
| CVE-2026-32071 | Windows Local Security Authority Subsystem Service (LSASS) Denial of Service Vulnerability | Exploitation Less Likely | No | 7.5 |
| CVE-2026-27929 | Windows LUA File Virtualization Filter Driver Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.0 |
| CVE-2026-20930 | Windows Management Services Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-26162 | Windows OLE Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-33101 | Windows Print Spooler Elevation of Privilege Vulnerability | Exploitation Unlikely | No | 7.8 |
| CVE-2026-32084 | Windows Print Spooler Information Disclosure Vulnerability | Exploitation Unlikely | No | 5.5 |
| CVE-2026-27927 | Windows Projected File System Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-26184 | Windows Projected File System Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-32069 | Windows Projected File System Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-32074 | Windows Projected File System Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-32078 | Windows Projected File System Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-26167 | Windows Push Notifications Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 8.8 |
| CVE-2026-32158 | Windows Push Notifications Elevation of Privilege Vulnerability | Exploitation Unlikely | No | 7.8 |
| CVE-2026-32159 | Windows Push Notifications Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-32160 | Windows Push Notifications Elevation of Privilege Vulnerability | Exploitation Unlikely | No | 7.8 |
| CVE-2026-26172 | Windows Push Notifications Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-20928 | Windows Recovery Environment Security Feature Bypass Vulnerability | Exploitation Less Likely | No | 4.6 |
| CVE-2026-32216 | Windows Redirected Drive Buffering System Denial of Service Vulnerability | Exploitation Less Likely | No | 5.5 |
| CVE-2026-27909 | Windows Search Service Elevation of Privilege Vulnerability | Exploitation More Likely | No | 7.8 |
| CVE-2026-26161 | Windows Sensor Data Service Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-26174 | Windows Server Update Service (WSUS) Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.0 |
| CVE-2026-32224 | Windows Server Update Service (WSUS) Elevation of Privilege Vulnerability | Exploitation Unlikely | No | 7.0 |
| CVE-2026-26154 | Windows Server Update Service (WSUS) Tampering Vulnerability | Exploitation Less Likely | No | 7.5 |
| CVE-2026-26165 | Windows Shell Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.0 |
| CVE-2026-26166 | Windows Shell Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.0 |
| CVE-2026-27918 | Windows Shell Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-32151 | Windows Shell Information Disclosure Vulnerability | Exploitation Less Likely | No | 6.5 |
| CVE-2026-32225 | Windows Shell Security Feature Bypass Vulnerability | Exploitation More Likely | No | 8.8 |
| CVE-2026-32202 | Windows Shell Spoofing Vulnerability | Exploitation More Likely | No | 4.3 |
| CVE-2026-32082 | Windows Simple Search and Discovery Protocol (SSDP) Service Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.0 |
| CVE-2026-32083 | Windows Simple Search and Discovery Protocol (SSDP) Service Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.0 |
| CVE-2026-32068 | Windows Simple Search and Discovery Protocol (SSDP) Service Elevation of Privilege Vulnerability | Exploitation Unlikely | No | 7.0 |
| CVE-2026-32183 | Windows Snipping Tool Remote Code Execution Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-33829 | Windows Snipping Tool Spoofing Vulnerability | Exploitation Unlikely | No | 4.3 |
| CVE-2026-32089 | Windows Speech Brokered Api Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-32090 | Windows Speech Brokered Api Elevation of Privilege Vulnerability | Exploitation Unlikely | No | 7.8 |
| CVE-2026-32153 | Windows Speech Runtime Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-27907 | Windows Storage Spaces Controller Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-32076 | Windows Storage Spaces Controller Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-33827 | Windows TCP/IP Remote Code Execution Vulnerability | Exploitation Less Likely | No | 8.1 |
| CVE-2026-27908 | Windows TDI Translation Driver (tdx.sys) Elevation of Privilege Vulnerability | Exploitation More Likely | No | 7.0 |
| CVE-2026-27921 | Windows TDI Translation Driver (tdx.sys) Elevation of Privilege Vulnerability | Exploitation More Likely | No | 7.0 |
| CVE-2026-27915 | Windows UPnP Device Host Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-27919 | Windows UPnP Device Host Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-32075 | Windows UPnP Device Host Elevation of Privilege Vulnerability | Exploitation More Likely | No | 7.0 |
| CVE-2026-27916 | Windows UPnP Device Host Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-27920 | Windows UPnP Device Host Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-32077 | Windows UPnP Device Host Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-27925 | Windows UPnP Device Host Information Disclosure Vulnerability | Exploitation Less Likely | No | 6.5 |
| CVE-2026-32156 | Windows UPnP Device Host Remote Code Execution Vulnerability | Exploitation Less Likely | No | 7.4 |
| CVE-2026-32223 | Windows USB Printing Stack (usbprint.sys) Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 6.8 |
| CVE-2026-32165 | Windows User Interface Core Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-27911 | Windows User Interface Core Elevation of Privilege Vulnerability | Exploitation Unlikely | No | 7.8 |
| CVE-2026-32163 | Windows User Interface Core Elevation of Privilege Vulnerability | Exploitation Unlikely | No | 7.8 |
| CVE-2026-32164 | Windows User Interface Core Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
| CVE-2026-23670 | Windows Virtualization-Based Security (VBS) Security Feature Bypass Vulnerability | Exploitation Less Likely | No | 5.7 |
| CVE-2026-32080 | Windows WalletService Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.0 |
| CVE-2026-27917 | Windows WFP NDIS Lightweight Filter Driver (wfplwfs.sys) Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.0 |
| CVE-2026-32222 | Windows Win32k Elevation of Privilege Vulnerability | Exploitation Less Likely | No | 7.8 |
CVE | Title | Exploitation status | Publicly disclosed? | CVSS v3 base score |
|---|---|---|---|---|
| CVE-2026-32201 | Microsoft SharePoint Server Spoofing Vulnerability | Exploitation Detected | No | 6.5 |
CVE | Title | Exploitation status | Publicly disclosed? | CVSS v3 base score |
|---|---|---|---|---|
| CVE-2026-33825 | Microsoft Defender Elevation of Privilege Vulnerability | Exploitation More Likely | Yes | 7.8 |
CVE | Title | Exploitation status | Publicly disclosed? | CVSS v3 base score |
|---|---|---|---|---|
| CVE-2026-33824 | Windows Internet Key Exchange (IKE) Service Extensions Remote Code Execution Vulnerability | Exploitation Less Likely | No | 9.8 |

Microsoft addressed 165 vulnerabilities affecting its various products and underlying systems, including one actively exploited vulnerability in Microsoft Office SharePoint, in this month’s Patch Tuesday update.
“By my count, this is the second-largest monthly release in Microsoft’s history,” Dustin Childs, head of threat awareness at Trend Micro’s Zero Day Initiative, wrote in a blog post Tuesday.
Microsoft didn’t explain why its monthly batch of patches grew so large this month, but Childs noted that many vulnerability programs are experiencing a significant increase in submissions found by artificial intelligence tools. “For us, our incoming rate has essentially tripled, making triage a challenge, to say the least,” he added.
The zero-day vulnerability — CVE-2026-32201 — has a CVSS rating of 6.5 and allows attackers to view sensitive information and make changes to disclosed information. Microsoft said the improper input validation defect in Microsoft Office SharePoint allows unauthenticated attackers to perform spoofing over a network.
The Cybersecurity and Infrastructure Security Agency added the zero-day to its known exploited vulnerabilities catalog shortly after Microsoft’s disclosure.
Microsoft also addressed a high-severity vulnerability — CVE-2026-33825 — that was publicly known at the time of release. The vendor said the defect in Microsoft Defender is more likely to be exploited and could allow unauthorized attackers to elevate privileges locally.
“What starts as a foothold can quickly become full system domination,” Jack Bicer, director of vulnerability research at Action1, said in a blog post about the vulnerability.
“Once exploited, it allows full control over endpoints, enabling data exfiltration, disabling security tools and lateral movement across networks,” Bicer said.
Proof-of-concept exploit code for the defect is publicly available, which increases the likelihood of exploitation in the wild, he added.
Microsoft disclosed two critical vulnerabilities this month — CVE-2026-33824 affecting Windows IKE Extension and CVE-2026-26149 affecting Microsoft Power Apps — but designated both of the defects as less likely to be exploited.
More than three-quarters of the vulnerabilities disclosed this month are less likely to be exploited, according to Microsoft. Meanwhile, the company designated 19 vulnerabilities as more likely to be exploited.
The full list of vulnerabilities addressed this month is available in Microsoft’s Security Response Center.
The post Microsoft drops its second-largest monthly batch of defects on record appeared first on CyberScoop.
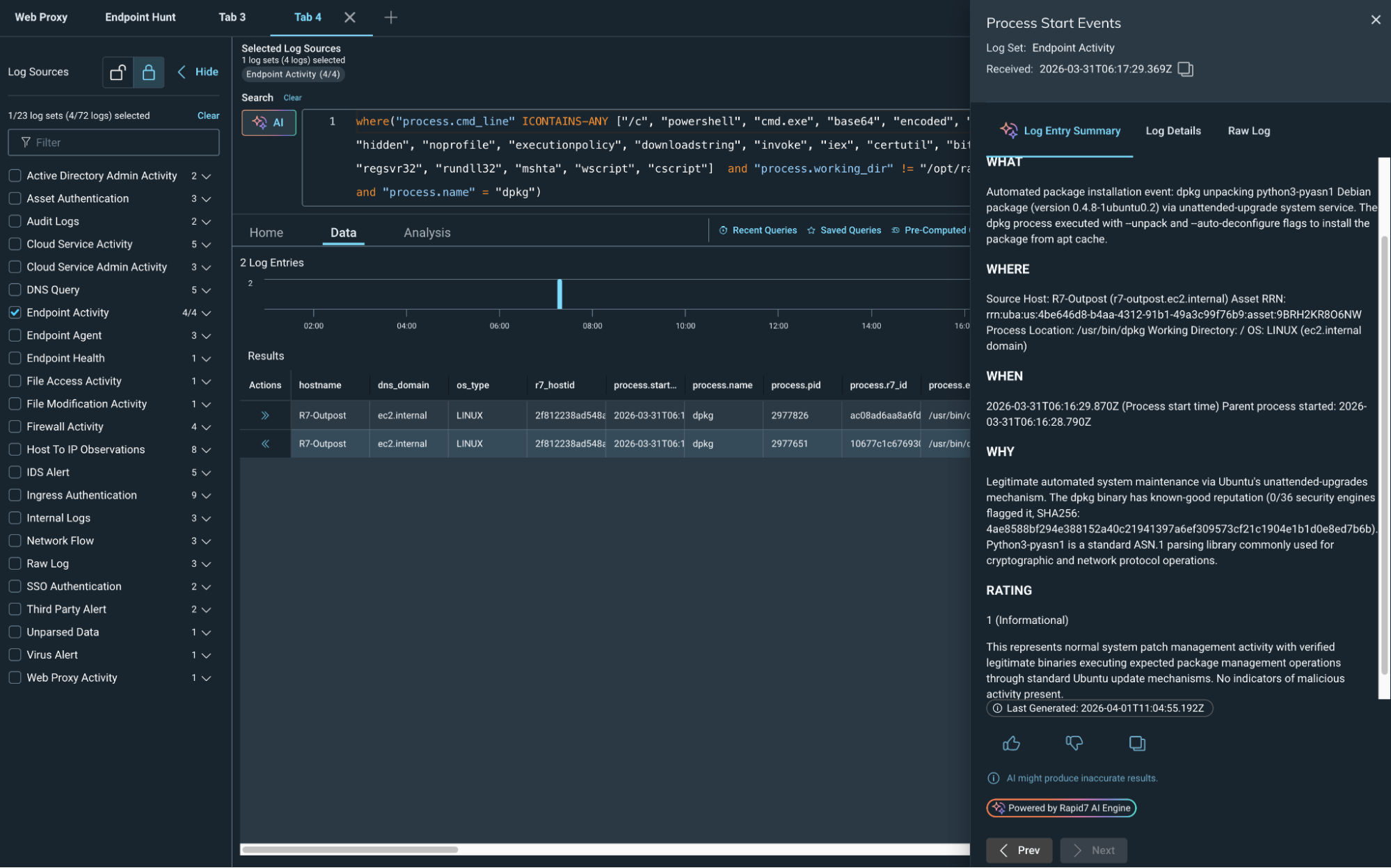
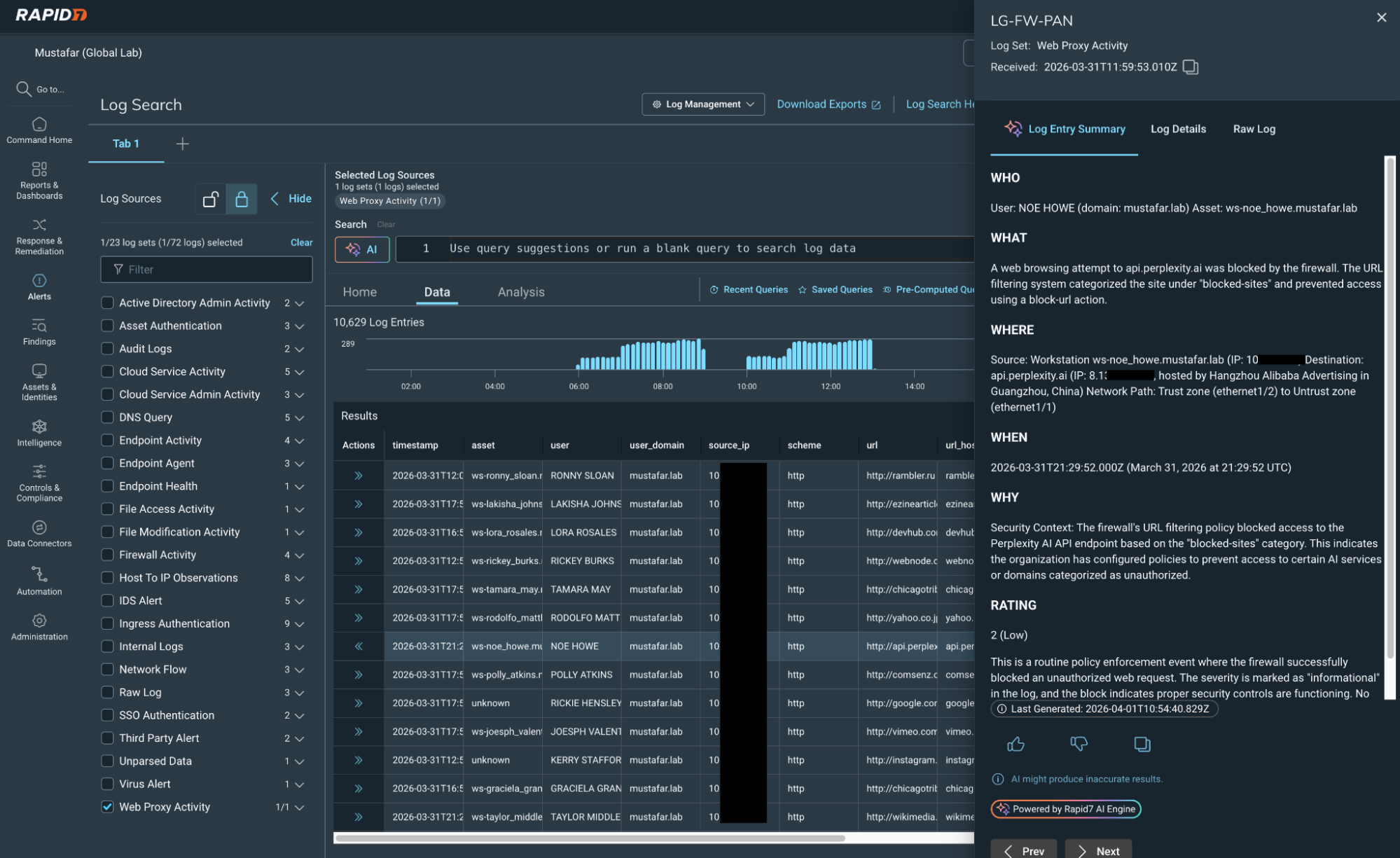
Security teams are flooded with logs, yet every alert demands fast, accurate context. In Verizon’s 2025 Data Breach Investigations Report [1], they analyzed 22,052 security incidents, of which 12,195 (55%) were confirmed breaches, underscoring how much activity teams must sift through to find what matters.
In practice, that means dozens of investigations per shift, each requiring fast judgment with incomplete context. A 2024 SANS survey shows that SOC teams report alert volume, limited context, and lack of automation continue to slow investigation and response [2].
Speed suffers. So does consistency.
AI-Powered Log Summary in Rapid7 Incident Command transforms raw log data into a clear, concise narrative directly within the investigation workflow. Analysts see what happened, why it matters, and what to do next in seconds, not minutes.
Instead of decoding logs line by line, analysts get:
Instant identification of who initiated the activity.
Fast understanding of exactly which actions occurred.
Clarity into when and where events unfolded.
Connectivity into why that behavior matters.
Analysts stay grounded in the original data, but they no longer have to fight through it to find answers. The summary provides immediate orientation and focus, keeping their focus on what to do next.
⠀
AI-Powered Log Summary is embedded directly into the log search workflow. No pivoting, and no context switching. With a single action, analysts generate a contextual summary tailored to their results in seconds. That means faster investigations without breaking flow.
Summaries can be shared with teammates or leadership to communicate findings quickly, without rewriting technical details into plain language. Everyone stays aligned on what happened and what comes next.
Rapid7 leverages the best available technology to protect our customers' attack surfaces. Our mission drives us to keep abreast of the latest AI advancements to deliver optimal value to customers while effectively managing the inherent risks of the technology. Integrating AI into our core processes enhances our operational security and underscores our commitment to ethical innovation.
At Rapid7, we are dedicated to leading responsibly in the AI space, ensuring that our technological advancements positively contribute to our customers, company, and society. Read more about how our TRiSM (Trust, Risk, and Security Management) is a foundational strategy that guides us in navigating the intricate landscape of AI with confidence and security.
By reducing time spent parsing logs, teams can focus on what matters: containment, remediation, and proactive threat hunting.
⠀
This brings analysts:
Faster triage and investigations.
More consistent analysis across shifts.
Lower cognitive load during high-volume periods.
Clear communication to stakeholders.
Rapid7 is at the vanguard of integrating AI into its products to accelerate outcomes for our customers, with a particular focus on amplifying analyst impact and bringing speed and clarity to SOC operations throughout the threat detection and response lifecycle.
That is how modern SOC teams move faster. Visit the Incident Command page for more information.
⠀
Other noteworthy stories that might have slipped under the radar: Jones Day hacked, Internet Bug Bounty program paused due to AI, new Mac stealer malware.
The post In Other News: Cyberattack Stings Stryker, Windows Zero-Day, China Supercomputer Hack appeared first on SecurityWeek.
Beyond monitoring and compliance, visibility acts as a powerful deterrent, shaping user behavior, improving collaboration, and enabling more accurate, data-driven security decisions.
The post The Hidden ROI of Visibility: Better Decisions, Better Behavior, Better Security appeared first on SecurityWeek.

Shadow AI embedded in everyday apps, combined with outdated mobile devices and zero-click exploits, is creating a new and largely unseen mobile risk.
The post Mobile Attack Surface Expands as Enterprises Lose Control appeared first on SecurityWeek.
This article explains why many breaches are driven by gaps in visibility rather than advanced exploits, how attackers move through modern environments, and what changes when organizations start connecting assets, identities, and attack paths into a single view.
A visibility problem exists when security teams cannot clearly answer three basic questions: what assets exist, who or what can access them, and how those elements connect. When those answers are incomplete, decisions are made based on assumptions – and that creates conditions where risk can grow, unnoticed.
As environments expand across cloud, SaaS, and hybrid infrastructure, the number of systems and identities grows quickly. What often falls behind is a clear understanding of how they relate to each other, and that gap is where attackers tend to operate.
A large medical technology organization experienced a breach driven by a series of compounding gaps rather than a single exploit. Internet-exposed assets created the initial entry point, while inconsistencies in device posture and identity enforcement, including gaps in platforms like Intune, weakened the security boundary. Attackers leveraged exposed or reused credentials and over-permissioned access to move laterally across systems. Without unified visibility across assets, identities, and managed devices, the attack path remained invisible until critical systems were reached.
Each of these conditions is common on its own, but what makes them dangerous is how they connect.
This breach did not rely on a zero-day vulnerability or an advanced technique. It depended on an exposed asset, valid credentials, and inconsistent enforcement across identity and devices. Those elements exist in most environments, but without visibility into how they overlap, they can be combined into a viable attack path.
Security teams often evaluate vulnerabilities individually, while attackers focus on how those weaknesses can be chained together. The risk is not just in what is vulnerable, but in how exposure allows movement.
Improving outcomes depends on understanding how exposure exists across the environment and how different elements relate to each other.
Asset visibility is the starting point. Many organizations cannot confidently identify everything that is externally accessible, and attackers often find assets that were never intended to be exposed. Continuously mapping assets across cloud and on-prem environments reduces that uncertainty and limits entry points.
Identity is just as critical. Once access is established, movement depends on credentials and permissions. Stolen credentials, over-permissioned accounts, and weak authentication paths allow attackers to move beyond initial entry. Treating identity exposure as part of the attack surface helps identify these risks earlier, especially when leaked credentials can be tied to active accounts and privileges.
Attack path visibility connects these elements. Instead of evaluating findings in isolation, it shows how exposures can be combined into realistic attack scenarios. Through adversarial simulation, organizations can observe how an attacker could move from an exposed system to internal resources, which shifts focus toward removing viable paths rather than addressing isolated issues.
External signals, such as credential leaks, only become meaningful when tied back to internal systems. Monitoring for exposed credentials is useful, but correlating those credentials with active accounts and access levels is what turns that signal into something actionable.
Controls such as least privilege and multi-factor authentication remain essential, but they are only effective when applied consistently. Without visibility into where access exists, enforcement gaps are difficult to detect.
The difference in a scenario like this is not simply better tooling. It is a shift in how exposure is understood and prioritized.
Attackers look for the easiest path through an environment. A visibility-first approach identifies those paths earlier, reduces them, and then examines why they existed. That changes how teams prioritize work, moving from reacting to individual findings toward removing viable attack paths.
This is where platforms like Rapid7 support a more complete view of exposure. Surface Command aggregates telemetry from over 190 sources, helping organizations unify fragmented views of assets and identities. InsightCloudSec extends that visibility into cloud environments by enforcing best practices and least privilege without relying on manual processes. Vector Command focuses on how attackers move, using continuous testing and simulation to show how attacks would unfold across an environment.
On the intelligence side, integrating threat data with identity systems allows external signals, such as credential leaks, to be mapped to active accounts and validated in real time. That makes it possible to act before those credentials are used.
Together, these capabilities provide a clearer understanding of how exposure translates into risk.
Zero trust depends on more than policy. It requires visibility, identity, validation, and enforcement to work together continuously.
Without visibility, zero trust becomes difficult to apply in practice. With it, security decisions can be based on how systems actually behave rather than how they are expected to behave, which shifts organizations away from reacting to incidents and toward preventing them from forming.

For years, cybersecurity professionals have relied on a familiar metric to dictate their day-to-day priorities: the Common Vulnerability Scoring System (CVSS). In today’s hyper-connected, sprawling IT environments, utilizing a static severity score as the ultimate arbiter of risk creates opportunities for threat actors. While defenders chase down theoretical, high-scoring alerts, adversaries are quietly targeting the truly exploitable, business-critical exposures that slip through the cracks.
In a recent report, Gartner® highlighted a projection:
"By 2028, organizations that prioritize exposures using threat intelligence, asset context, exploitability modeling and security control validation will reduce breach likelihood by at least 70% compared to peers relying primarily on CVSS-based vulnerability prioritization." [1]
This affirms what many seasoned practitioners have suspected for years: there’s an abundance of vulnerability findings, but a lack of actionable context.
Most vulnerability management programs evolved during a time when the attack surface was relatively static, adversary tooling was rudimentary, and remediation capacity generally exceeded the volume of new disclosures. Today, enterprises are confronted with vulnerabilities scattered across complex cloud architectures, SaaS applications, and intricate supply chains.
In this modern threat landscape, CVSS alone is insufficient because it measures theoretical severity, does not factor in whether an attacker is actually using the vulnerability in the wild, or consider the business value of any affected assets. According to Gartner®, fewer than 10% of vulnerabilities are exploited, yet most are treated as urgent [1]. This all leads to prioritization paralysis, where security teams spend countless hours patching vulnerabilities that pose low material risk to the business. The legacy approach rewards what is auditable rather than what is genuinely impactful.
To break free from endless patching and ineffective risk reduction practices, security professionals are shifting toward a context-driven model. As Gartner notes, strong exposure prioritization requires integrating four critical elements: threat intelligence, asset context, data science, and security control validation. Organizations are approaching these elements in a few practical ways:
Instead of just asking how severe a vulnerability is, modern exposure management asks whether an exposure is relevant to a threat actor who is capable of exploiting it right now. By embedding threat intelligence into each vulnerability finding, teams shift the focus from theoretical to risk active exploitation. It introduces the adversary's perspective by identifying known exploited vulnerabilities, public or private exploit availability, and targeted campaigns. By filtering out exposures with no evidence of attacker interest, organizations can instantly collapse large vulnerability backlogs and focus only on relevant threats.
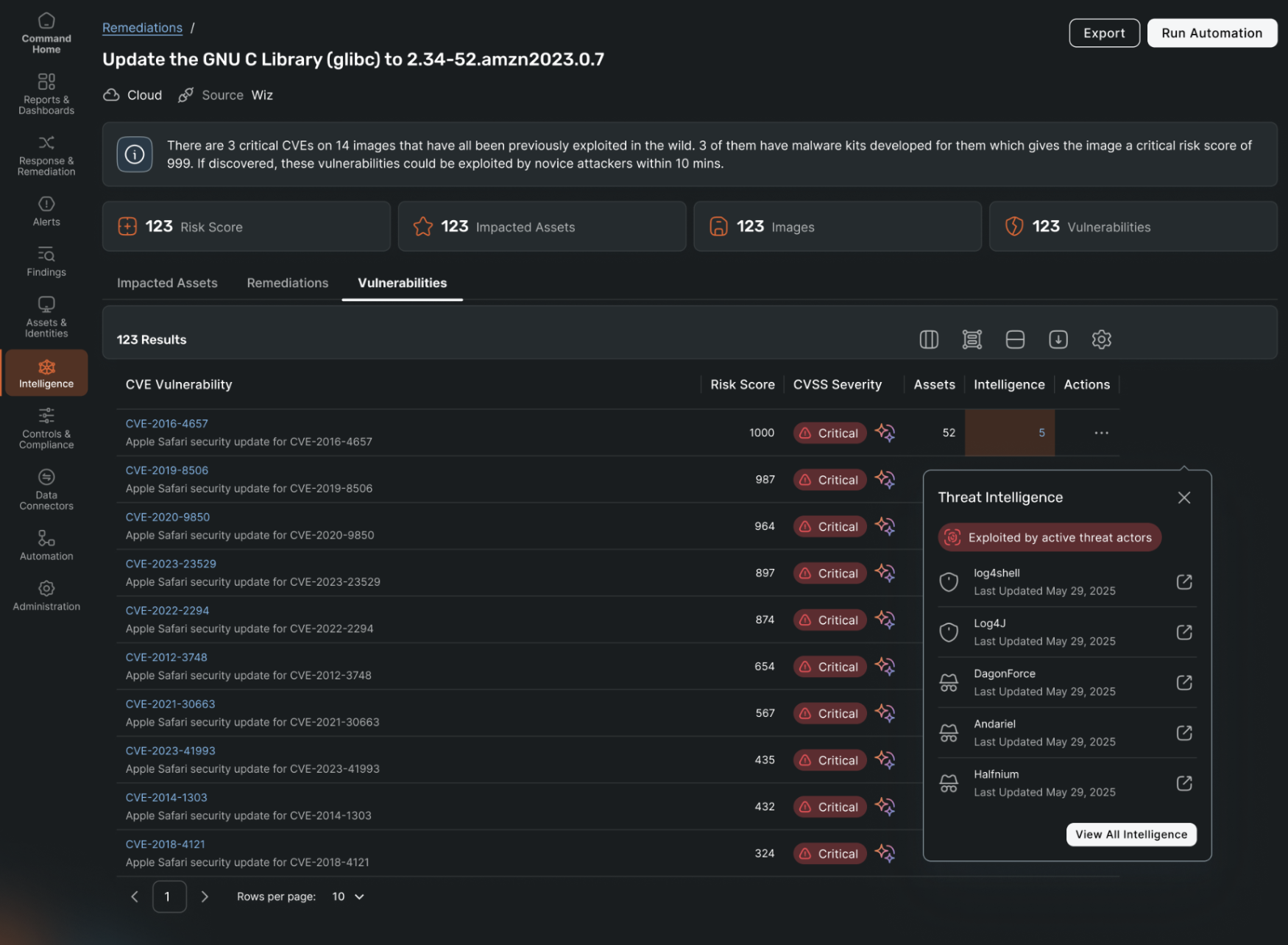
Not all assets are created equal. A critical vulnerability on an isolated, internal test server is vastly different from the same vulnerability on a public-facing cloud workload processing customer sensitive data. Asset context enriches exposure data with crucial business information: what the asset is, its external accessibility, and its relationship to core business functions. Without this context, security teams waste disproportionate effort on low-impact systems, treating every critical alert as an equal emergency.
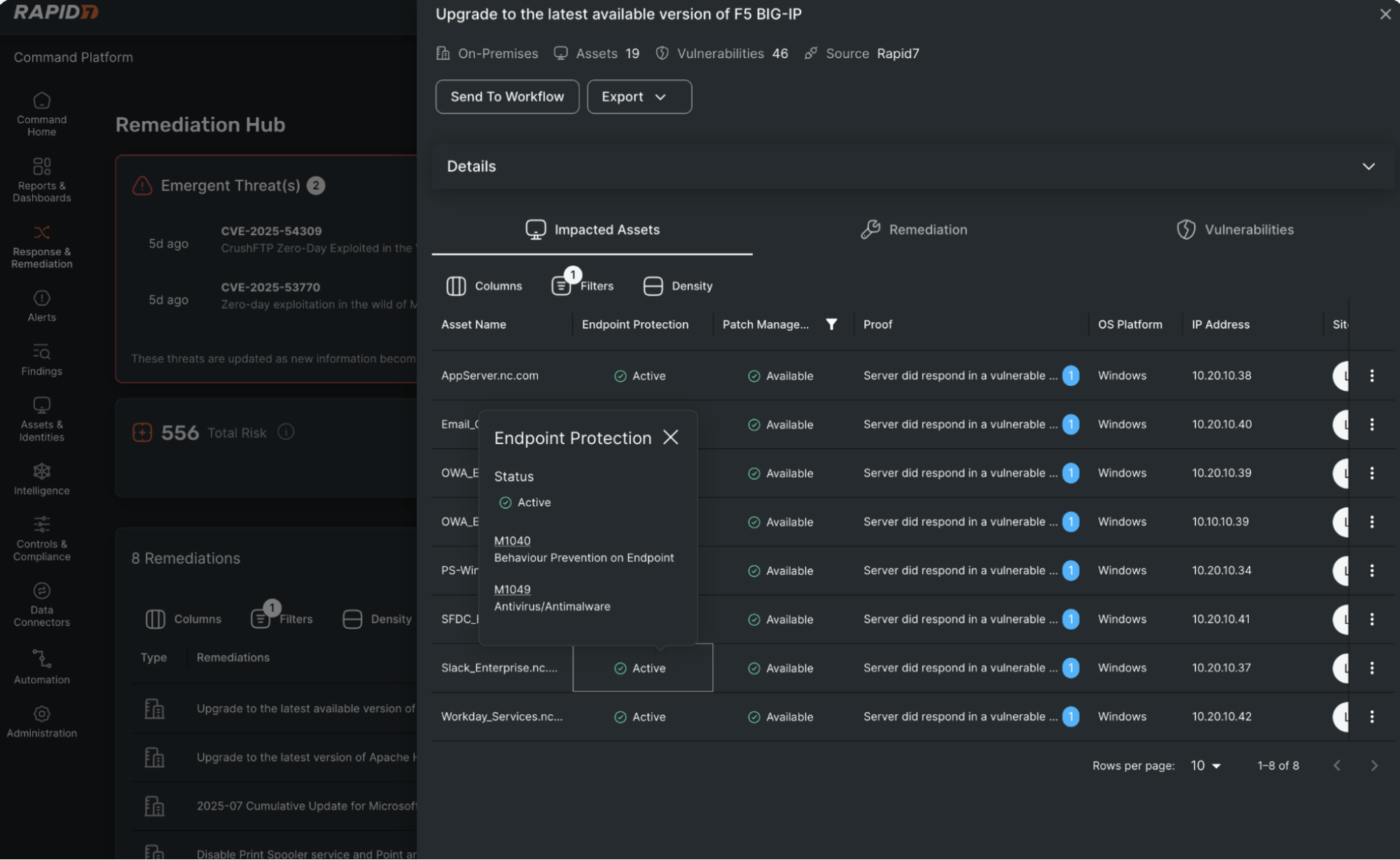
Security analysts often struggle to assess exploitability given the overwhelming volume of vulnerabilities. By using predictive models like the Exploit Prediction Scoring System (EPSS), organizations can analyze large datasets of historical exploitation to identify latent risks. Exposure assessment platforms should display this data alongside each exposure finding to make it easier to predict the vulnerabilities most likely to become attacks.
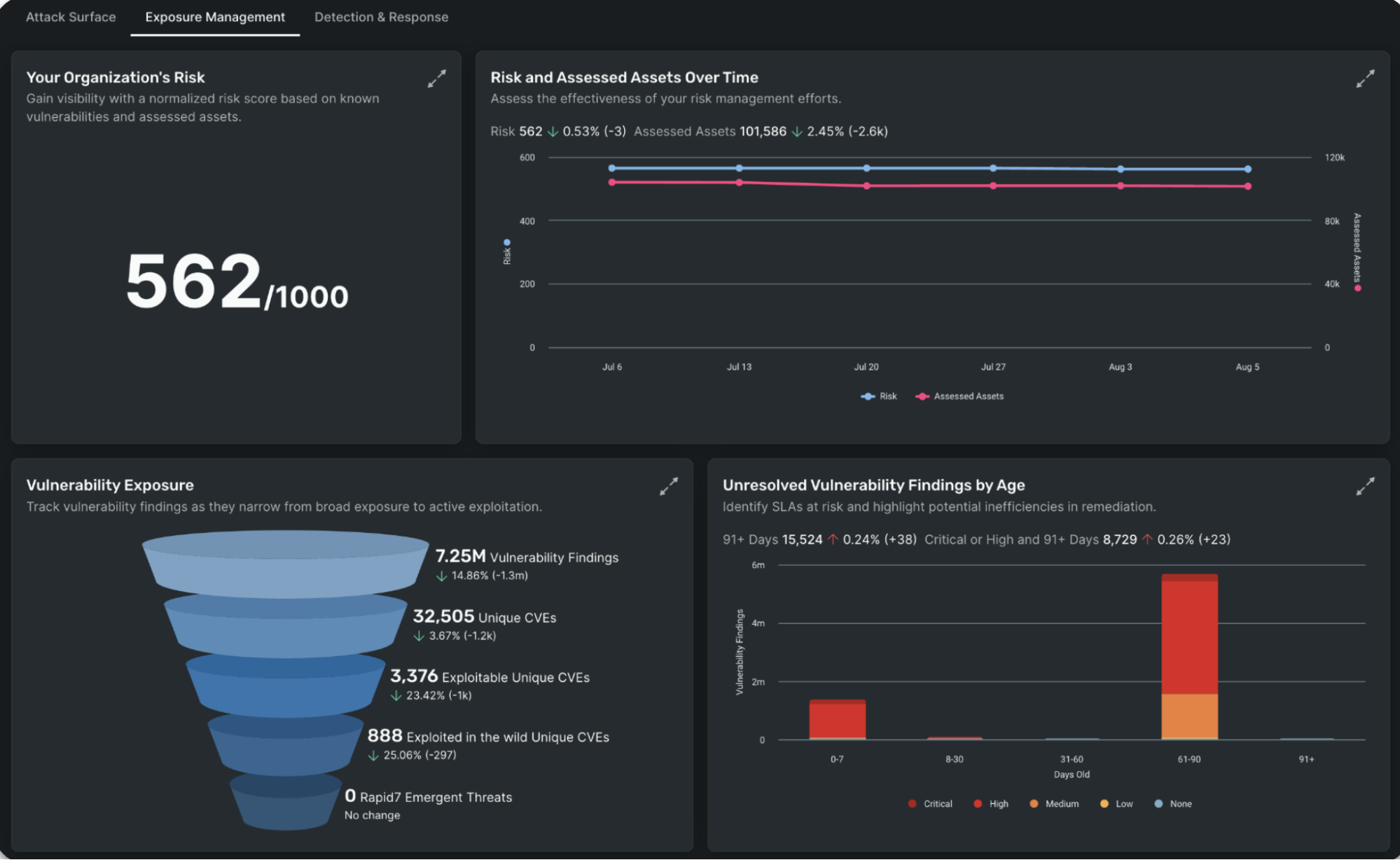
An exposure that appears highly exploitable in theory might be neutralized by existing defenses. By integrating security and policy controls, you can evaluate exposures in the context of endpoint protection and identity management. This passive validation confirms whether an attacker can realistically exploit the exposure in your specific environment.
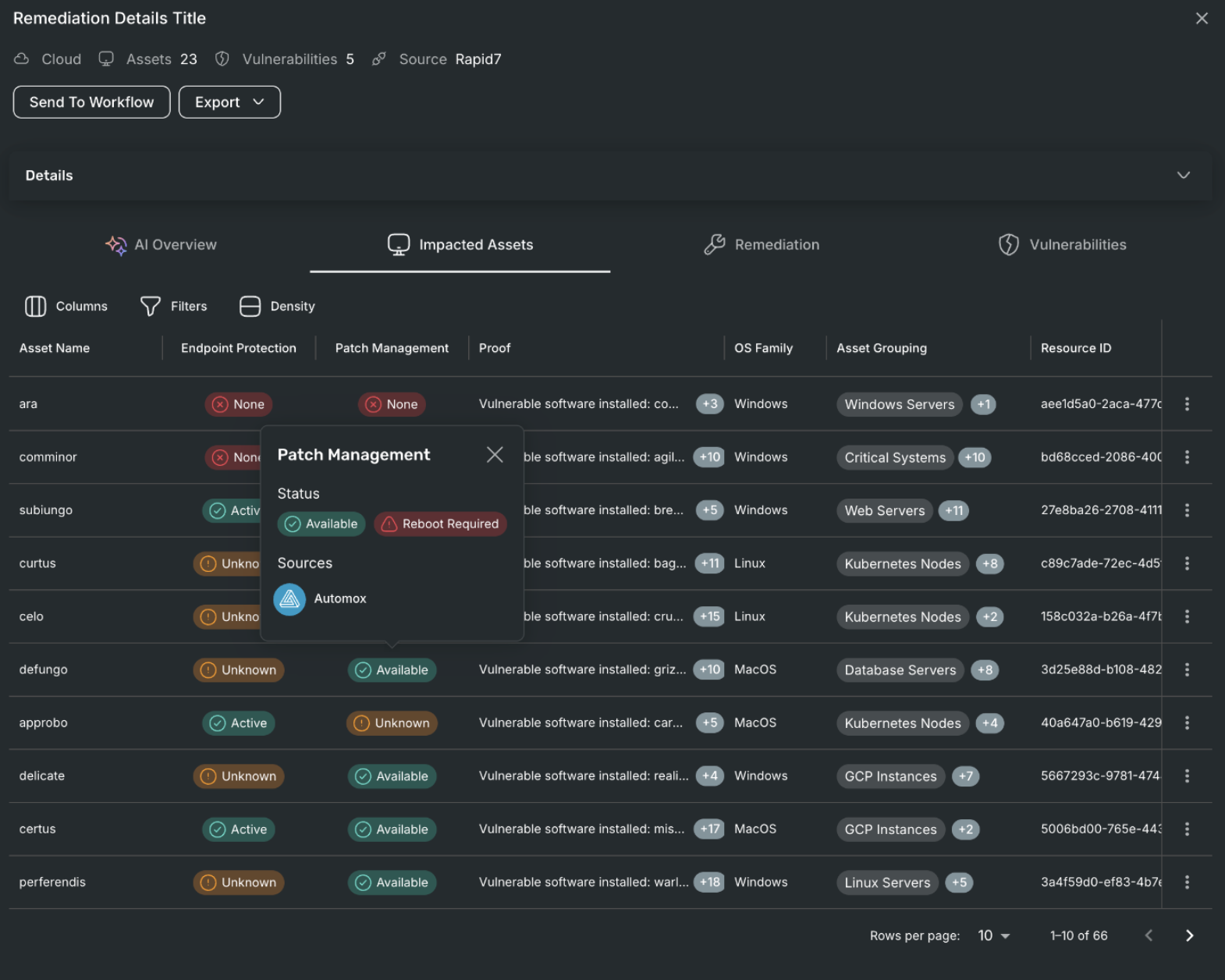
Individually, each element highlighted above provides incremental value, but when integrated, they fundamentally transform how prioritization decisions are made. This integrated model ensures that remediation efforts are mobilized only after priorities have been validated in the context of the business and the current threat landscape. It transitions vulnerability management from a purely technical, tool-centric exercise into a strategic, process-driven risk decision.
Security leaders must measure success not by the sheer number of vulnerabilities closed, but by the demonstrable reduction of exploitable exposures and the alignment of remediation efforts with actual attacker behavior. Operationalizing these four elements requires a unified platform that eliminates the silos between vulnerability management, cloud security, and threat intelligence. You cannot manually stitch together disconnected spreadsheets and hope to outpace modern adversaries. This is where forward-thinking organizations are leaning on comprehensive, end-to-end solutions like Rapid7 Exposure Command that seamlessly aggregate visibility across on-premises and dynamic cloud environments. With deep, native integration of Rapid7 Cloud Security capabilities, teams can instantly map asset criticality and external accessibility within complex, ephemeral cloud architectures. Furthermore, by infusing world-class threat intelligence and active exploit data directly into exposure findings, Rapid7 enables security teams to cut through the noise, validate security controls, and pinpoint the exact exposures that matter most—all with minimal friction.
[1] Gartner, Prioritize What Attackers Will Exploit: 4 Elements of Strong Exposure Prioritization, Jonathan Nunez, 5 March 2026.

The ban aligns with a White House determination that all routers produced abroad are a threat to national security.
The post FCC Bans New Routers Made Outside the US Over National Security Risks appeared first on SecurityWeek.
Security leaders rarely struggle to produce data. The challenge is turning that data into something the board can use to make decisions.
Walk into a board meeting with a slide showing 1,200 critical vulnerabilities and 44 internet-facing assets, and you will likely see polite acknowledgment rather than meaningful discussion. The question that follows tends to cut through quickly: what does this mean for the business?
Boards allocate capital based on financial exposure, not vulnerability counts. A list of findings describes workload, but directors are responsible for revenue protection, liability, and risk to the balance sheet. When security reporting remains technical, it sits outside the way investment decisions are made elsewhere in the organization. The issue is less about communication and more about framing the problem in terms the business already understands.
CVSS measures theoretical severity, but it does not measure business risk. A high score indicates that a flaw could be dangerous, yet it does not tell you whether the vulnerability is reachable in your environment, whether exploit code exists, or whether it is likely to affect revenue in the near term. It answers a useful engineering question, but it does not answer the question the board is asking.
That question is about likelihood and impact. Most enterprise risk frameworks define risk in those terms, and that is how financial decisions are made. The gap becomes clear when two vulnerabilities appear similar on a dashboard but carry very different consequences. A high-CVSS issue on a segmented lab system may present little business risk, while a moderately severe vulnerability on an internet-facing production system with active exploit activity can expose regulated data and revenue streams.
What is often missing in that comparison is threat context. Understanding how attackers behave, which vulnerabilities they are exploiting, and where access paths actually exist changes how risk is interpreted. Active Risk in InsightVM brings those elements together by combining exploit telemetry, attacker behavior, and asset context to estimate the likelihood that a vulnerability will be used. When that likelihood is paired with business impact, the conversation shifts toward exposure rather than severity.
Prioritization alone does not translate into board-level decisions. Knowing what is most likely to be exploited is necessary, but it is not sufficient when the goal is to justify investment.
FAIR provides a way to bridge that gap. The model defines risk as a combination of how often a loss event is likely to occur and how much that event would cost. In practical terms:
Annualized Loss Exposure (ALE) = Loss Event Frequency × Probable Loss Magnitude
Active Risk informs the likelihood side of that equation by grounding it in observed attacker behavior and exploit activity. FAIR converts that likelihood into financial terms, allowing security teams to describe exposure in a way that aligns with how capital is allocated.
Instead of reporting that a set of vulnerabilities is “high risk,” the discussion becomes more concrete. A team might say that a group of issues represents several million dollars in annualized exposure across systems tied to revenue. That is a number that can be evaluated alongside other business risks, rather than interpreted as a technical signal.
Consider two vulnerabilities identified during a scan. The first is a CVSS 9.8 issue on a segmented guest Wi-Fi router. It is severe from a technical standpoint, but it has no access to sensitive data, no path into production systems, and no evidence of active exploitation.
The second is a vulnerability with a moderate CVSS score on an internet-facing customer database. Public exploit code exists, and the system stores regulated data tied directly to revenue and compliance obligations.
On a scanner dashboard, the first may appear more urgent. When viewed through a financial lens, the second carries greater risk.
Assume an annual probability of exploitation of 20 percent for the database scenario. If the potential impact includes $750,000 in incident response, $1.2 million from several days of business interruption, $600,000 in legal and regulatory costs, and $1 million in customer churn and reputational damage, the total loss for a single event is $3.55 million.
Applying the FAIR model results in approximately $710,000 in annualized exposure. That figure reflects the risk carried by that single vulnerability on a production system.
By contrast, even if the Wi-Fi router vulnerability had a 5 percent probability of exploitation and a $50,000 impact, the resulting exposure would be around $2,500. Both findings may appear critical in a technical report, but only one represents a material financial concern.
This is where Active Risk and FAIR work together. One identifies where attackers are likely to act, and the other expresses the consequence in financial terms. The combination changes how vulnerabilities are evaluated and how priorities are set.
Once risk is expressed in financial terms, the next step is to understand how that exposure is distributed. Boards tend to think in terms of portfolios rather than individual issues, and the same principle applies to cybersecurity.
In most environments, exposure is not evenly spread. A relatively small number of systems and vulnerabilities account for a large portion of potential loss. Internet-facing services, systems tied to revenue, and assets with known exploit activity often sit at the higher end of that distribution.
This creates a practical way to focus effort. Rather than attempting to address every vulnerability equally, teams can identify where exposure is concentrated and reduce risk in those areas first. In many cases, addressing a small number of issues can significantly reduce overall exposure, particularly when those issues sit on systems that are both reachable and business-critical.
A before-and-after view helps make this visible. If an organization reduces modeled exposure from several million dollars to a substantially lower figure through targeted remediation, the result can be explained in terms of reduced downside risk rather than increased patching activity. Over time, tracking that change shows whether investments are producing measurable outcomes.
By the time exposure is expressed in financial terms, the discussion in the boardroom has already shifted. The focus moves away from counts and severity toward risk, trade-offs, and acceptable levels of exposure.
One of the first issues that arises in that context is the assumption that risk should be driven to zero. In practice, eliminating all exposure is neither achievable nor economically sensible. Reducing risk always involves trade-offs, and those trade-offs become clearer when expressed in financial terms.
If an organization has already reduced exposure significantly, but further reduction requires a disproportionate increase in cost, the decision becomes one of balance. The question is no longer why risk still exists, but whether the remaining exposure aligns with the organization’s tolerance.
The same logic applies when discussing budget. Requests framed in operational terms, such as additional headcount or tooling, are difficult to evaluate in isolation. When those requests are tied to measurable reductions in exposure, the relationship between cost and benefit becomes clearer.
For example, if additional resources reduce several million dollars of modeled exposure at a fraction of that cost, the investment can be assessed alongside other initiatives using the same financial lens. At that point, the discussion is no longer about capacity. It is about risk reduction.
Reducing exposure also affects how the organization is perceived externally. Cyber insurance underwriting, for example, increasingly considers factors such as attack surface, exploit availability, and remediation speed. Demonstrating that exposure is measured and reduced over time can influence how risk is priced.
The same applies during customer due diligence. Being able to explain where risk exists, how it is prioritized, and how it has been reduced provides evidence of maturity. It shows that security is being managed deliberately rather than reactively.
Productive board discussions tend to end with agreement on acceptable levels of exposure. Without a financial view, every issue can appear urgent. With it, prioritization becomes more grounded.
Leadership can evaluate whether the level of risk being carried is consistent with business objectives, and whether further investment is warranted. That shifts vulnerability management from a process focused on volume to one focused on where exposure is concentrated and how it can be reduced most effectively.
Vulnerability management has often been treated as an operational activity centered on patching and scanning. When combined with threat context and financial modeling, it becomes part of enterprise risk management.
Instead of reporting how many vulnerabilities exist, security leaders can describe how much exposure the organization carries. Instead of focusing on activity, they can show how targeted actions reduce risk over time. That framing aligns cybersecurity with the same decision-making process used across the rest of the business.
When exposure is clear, decisions become clearer. Leadership can determine where to accept risk, where to transfer it, and where to invest in reduction. The conversation with the board moves away from technical detail and toward measurable impact, which is where security becomes part of strategy rather than an isolated function.

Researchers and threat hunters are scrambling to contain a maximum-severity defect in Ubiquiti’s UniFi Network Application that attackers could exploit to take over user accounts by accessing and manipulating files.
The path-traversal vulnerability — CVE-2026-22557 — affects software used to manage UniFi networking devices, including access points, gateways and switches. The vendor disclosed and released patches for the defect in a security advisory Wednesday.
“As of this morning, we have not observed any public proof-of-concept exploits or confirmed reports of exploitation in the wild,” Matthew Guidry, senior product detection engineer at Censys, told CyberScoop.
“However, because this is a path-traversal vulnerability, the technical complexity for an attacker is typically lower than memory-corruption or buffer-overflow bugs,” he added. “Given that the CVSS 10 rating implies low attack complexity, we anticipate that once the specific vulnerable endpoint is identified, exploitation will be trivial to automate.”
Censys sensors observed nearly 88,000 UniFi Network Application hosts publicly exposed to the internet as of Friday morning. The software doesn’t expose what version it’s running, so scans cannot distinguish between vulnerable and patched instances.
Roughly one-third of the exposed instances of UniFi Network Application are located in the United States.
As a defender, when you see a CVSS 10 for a product you immediately recognize and know is everywhere, you probably get a bit anxious,” Guidry said. “You also know it’s remotely exploitable, requires no authentication, and needs no user interaction, because it wouldn’t be a 10 if it wasn’t. Ubiquiti is a name you hear frequently, and many of those devices are sitting directly on the internet.”
Ubiquiti advises UniFi Network Application users to update to the latest software versions, which also addressed a second vulnerability — CVE-2026-22558 — that attackers could exploit to escalate privileges.
The post Ubiquiti defect poses account takeover risk for UniFi Networking Application users appeared first on CyberScoop.
Cisco customers have confronted a flood of actively exploited vulnerabilities affecting the vendor’s network edge software since late February, and researchers say that five of the nine vulnerabilities Cisco disclosed in its firewalls and SD-WAN systems over the past three weeks have already been exploited in the wild.
Attackers exploited a pair of these defects — zero-day vulnerabilities in Cisco SD-WANs — for at least three years before the vendor and authorities discovered and issued warnings about the threat. Cisco disclosed an additional five SD-WAN vulnerabilities that same day, and three of those defects have since been confirmed actively exploited as well.
Weaknesses lurking in Cisco security products don’t end there. Amazon Threat Intelligence on Wednesday said one of the two max-severity defects Cisco reported in its firewall management software earlier this month has been actively exploited by Interlock ransomware since Jan. 26, more than a month before those vulnerabilities were publicly disclosed.
Some organizations, officials and members of the security community at large have missed widening risks as more of the defects come under attack. The flurry of Cisco SD-WAN and firewall vulnerabilities includes defects with low CVSS ratings, zero-days and others that were determined actively exploited after disclosure.
“These are not random bugs in low-value software. These are management-plane and control-plane weaknesses in devices at the network edge, which often function as trust anchors in enterprise environments,” Douglas McKee, director of vulnerability intelligence at Rapid7, told CyberScoop.
“If you compromise SD-WAN or firewall management, you’re landing on policy, visibility, routing, segmentation, and, in many cases, administrative trust over a large swath of the environment,” he added. “Attackers know that and, when they find a pre-auth path into those systems, especially one that can be chained to root, that’s about as attractive as it gets.”
The full slate of recently disclosed Cisco vulnerabilities affecting these systems include:
Researchers from multiple firms and Cisco have observed or been notified of active exploitation of CVE-2026-20127, CVE-2022-20775, CVE-2026-20122, CVE-2026-20128 and CVE-2026-20131.
The Cybersecurity and Infrastructure Security Agency has only added two of the defects — CVE-2022-20775 and CVE-2026-20127 — to its known exploited vulnerabilities catalog thus far. The agency, which last week added new hunting and reporting requirements to an emergency directive it issued for the defects in late February, did not answer questions about the updated order or explain why other actively exploited Cisco vulnerabilities haven’t been added to the catalog. The agency has been operating under a funding shutdown since February.
The ongoing ransomware campaign Amazon Threat Intelligence spotted involving CVE-2026-20131 confirmed “Interlock had a zero-day in their hands, giving them a week’s head start to compromise organizations before defenders even knew to look,” researchers said Wednesday.
Interlock’s observed attack path and operations are extensive, including post-compromise reconnaissance scripts, custom remote access trojans, a webshell and legitimate tool abuse. Amazon did not identify specific victims, and said the group threatens organizations with data encryption, regulatory fines and compliance valuations.
“Interlock has historically targeted specific sectors where operational disruption creates maximum pressure for payment,” Amazon Threat Intelligence researchers said in the blog post. These sectors include education, engineering, architecture, construction, manufacturing, industrial, health care and government entities.
The swarm of vulnerabilities in Cisco SD-WANs poses additional risk for customers. Cisco Talos previously attributed long-running attacks involving CVE-2026-20127 and CVE-2022-20775 to UAT-8616, but it’s unclear if the same threat group is responsible for all of the Cisco SD-WAN exploits.
“Other threat groups are likely to pick up public research in order to weaponize or adapt it opportunistically, so we may see follow-on attempts by additional threat actors, including low-skilled attackers,” Caitlin Condon, vice president of security research at VulnCheck, told CyberScoop.
Researchers said vulnerabilities are often disclosed in clusters after a meaningful defect is identified in a specific product, such as Cisco’s SD-WAN systems.
Cisco declined to answer questions and said customers can find the latest information on its security advisories page.
Condon and McKee both noted that Cisco has been responsive in releasing software fixes, threat-hunting intelligence and, in the case of the SD-WAN zero-days, coordinated government guidance.
“This is what a good crisis response is supposed to look like once exploitation is identified,” McKee said.
“The harder question is whether the industry is getting early-enough visibility into the defects in edge-management software that sophisticated actors are clearly prioritizing,” he added. “Are our organizations equipped with the right people and tools to perform this level of exposure management?”
The expanding exploits Cisco customers are combating on firewalls and SD-WANs is a reminder that organizations shouldn’t deprioritize less notorious vulnerabilities or those with lower CVSS scores, Condon said.
“Several of the exploited vulnerabilities in this tranche of Cisco SD-WAN bugs don’t have critical CVSS scores, meaning teams using CVSS as a prioritization mechanism might miss medium- or high-scored flaws that still have real-world adversary utility,” she added.
The attacks also collectively reflect a persistent pattern of attackers targeting network edge systems from multiple vendors, including Cisco.
“Attackers continue to treat network edge and management infrastructure as prime real estate, and when defenders see pre-authentication, management-plane flaws with evidence of pre-disclosure exploitation, they need to assume compromise, not just exposure,” McKee said.
“Attackers are investing time and capability into finding and operationalizing previously unknown defects in Cisco edge and management infrastructure because the payoff is enormous,” he added. “These platforms give you a privileged position, broad visibility, and a path to durable access inside high-value organizations. That’s exactly why they keep getting hit.”
The post Cisco’s latest vulnerability spree has a more troubling pattern underneath appeared first on CyberScoop.