Reading view
A little weak on being right
Microsoft Patch Tuesday, December 2025 Edition
Microsoft today pushed updates to fix at least 56 security flaws in its Windows operating systems and supported software. This final Patch Tuesday of 2025 tackles one zero-day bug that is already being exploited, as well as two publicly disclosed vulnerabilities.

Despite releasing a lower-than-normal number of security updates these past few months, Microsoft patched a whopping 1,129 vulnerabilities in 2025, an 11.9% increase from 2024. According to Satnam Narang at Tenable, this year marks the second consecutive year that Microsoft patched over one thousand vulnerabilities, and the third time it has done so since its inception.
The zero-day flaw patched today is CVE-2025-62221, a privilege escalation vulnerability affecting Windows 10 and later editions. The weakness resides in a component called the “Windows Cloud Files Mini Filter Driver” — a system driver that enables cloud applications to access file system functionalities.
“This is particularly concerning, as the mini filter is integral to services like OneDrive, Google Drive, and iCloud, and remains a core Windows component, even if none of those apps were installed,” said Adam Barnett, lead software engineer at Rapid7.
Only three of the flaws patched today earned Microsoft’s most-dire “critical” rating: Both CVE-2025-62554 and CVE-2025-62557 involve Microsoft Office, and both can exploited merely by viewing a booby-trapped email message in the Preview Pane. Another critical bug — CVE-2025-62562 — involves Microsoft Outlook, although Redmond says the Preview Pane is not an attack vector with this one.
But according to Microsoft, the vulnerabilities most likely to be exploited from this month’s patch batch are other (non-critical) privilege escalation bugs, including:
–CVE-2025-62458 — Win32k
–CVE-2025-62470 — Windows Common Log File System Driver
–CVE-2025-62472 — Windows Remote Access Connection Manager
–CVE-2025-59516 — Windows Storage VSP Driver
–CVE-2025-59517 — Windows Storage VSP Driver
Kev Breen, senior director of threat research at Immersive, said privilege escalation flaws are observed in almost every incident involving host compromises.
“We don’t know why Microsoft has marked these specifically as more likely, but the majority of these components have historically been exploited in the wild or have enough technical detail on previous CVEs that it would be easier for threat actors to weaponize these,” Breen said. “Either way, while not actively being exploited, these should be patched sooner rather than later.”
One of the more interesting vulnerabilities patched this month is CVE-2025-64671, a remote code execution flaw in the Github Copilot Plugin for Jetbrains AI-based coding assistant that is used by Microsoft and GitHub. Breen said this flaw would allow attackers to execute arbitrary code by tricking the large language model (LLM) into running commands that bypass the user’s “auto-approve” settings.
CVE-2025-64671 is part of a broader, more systemic security crisis that security researcher Ari Marzuk has branded IDEsaster (IDE stands for “integrated development environment”), which encompasses more than 30 separate vulnerabilities reported in nearly a dozen market-leading AI coding platforms, including Cursor, Windsurf, Gemini CLI, and Claude Code.
The other publicly-disclosed vulnerability patched today is CVE-2025-54100, a remote code execution bug in Windows Powershell on Windows Server 2008 and later that allows an unauthenticated attacker to run code in the security context of the user.
For anyone seeking a more granular breakdown of the security updates Microsoft pushed today, check out the roundup at the SANS Internet Storm Center. As always, please leave a note in the comments if you experience problems applying any of this month’s Windows patches.
Commonly Abused Administrative Utilities: A Hidden Risk to Enterprise Security
Organizations tend to focus a significant amount of their efforts on external threats, such as phishing and ransomware, but they often overlook one of the most dangerous attack vectors on their internal networks.
The post Commonly Abused Administrative Utilities: A Hidden Risk to Enterprise Security appeared first on Black Hills Information Security, Inc..
Constrained Language Mode Bypass When __PSLockDownPolicy Is Used
Carrie Roberts // PowerShell’s Constrained Language (CLM) mode limits the functionality available to users to reduce the attack surface. It is meant to be used in conjunction with application control […]
The post Constrained Language Mode Bypass When __PSLockDownPolicy Is Used appeared first on Black Hills Information Security, Inc..
Webcast: Sacred Cash Cow Tipping 2020
Want to learn how attackers bypass endpoint products? Slides for this webcast can be found here: https://www.blackhillsinfosec.com/wp-content/uploads/2020/09/SLIDES_SacredCashCowTipping2020.pdf 3:41 – Alternate Interpreters 9:19 – Carbon Black Config Issue 15:07 – Cisco […]
The post Webcast: Sacred Cash Cow Tipping 2020 appeared first on Black Hills Information Security, Inc..
Webcast: Group Policies That Kill Kill Chains

On this webcast, we’ll guide you through an iterative process of building and deploying effective and practical Group Policy Objects (GPOs) that increase security posture. Slides for this webcast can […]
The post Webcast: Group Policies That Kill Kill Chains appeared first on Black Hills Information Security, Inc..
Check-LocalAdminHash & Exfiltrating All PowerShell History
Beau Bullock // TL;DR Check-LocalAdminHash is a new PowerShell script that can check a password hash against multiple hosts to determine if it’s a valid administrative credential. It also has […]
The post Check-LocalAdminHash & Exfiltrating All PowerShell History appeared first on Black Hills Information Security, Inc..
BHIS PODCAST: Endpoint Security Got You Down? No PowerShell? No Problem.

Do your PowerShell scripts keep getting caught? Tired of dealing with EDRs & Windows Defender every time you need to pop a box? In this one-hour podcast, originally recorded as […]
The post BHIS PODCAST: Endpoint Security Got You Down? No PowerShell? No Problem. appeared first on Black Hills Information Security, Inc..
Webcast: Endpoint Security Got You Down? No PowerShell? No Problem.

Do your PowerShell scripts keep getting caught? Tired of dealing with EDRs & Windows Defender every time you need to pop a box? In this one-hour webcast, we introduce a somewhat […]
The post Webcast: Endpoint Security Got You Down? No PowerShell? No Problem. appeared first on Black Hills Information Security, Inc..
Getting PowerShell Empire Past Windows Defender
Carrie Roberts //* (Updated 2/12/2020) ADVISORY: The techniques and tools referenced within this blog post may be outdated and do not apply to current situations. However, there is still potential […]
The post Getting PowerShell Empire Past Windows Defender appeared first on Black Hills Information Security, Inc..
PowerShell w/o PowerShell Simplified
Brian Fehrman // In a previous post, titled PowerShell without PowerShell, we showed you how you can bypass Application Whitelisting Software (AWS), PowerShell restrictions/monitoring, and Command Prompt restrictions. In some […]
The post PowerShell w/o PowerShell Simplified appeared first on Black Hills Information Security, Inc..
Are You Spying on me? Detecting SSL Man-in-the-Middle

Carrie Roberts//* Is your employer reading all your sensitive information when you browse the internet from your work computer? Probably. But how can you be sure? It is common for […]
The post Are You Spying on me? Detecting SSL Man-in-the-Middle appeared first on Black Hills Information Security, Inc..
Hide Payload in MS Office Document Properties
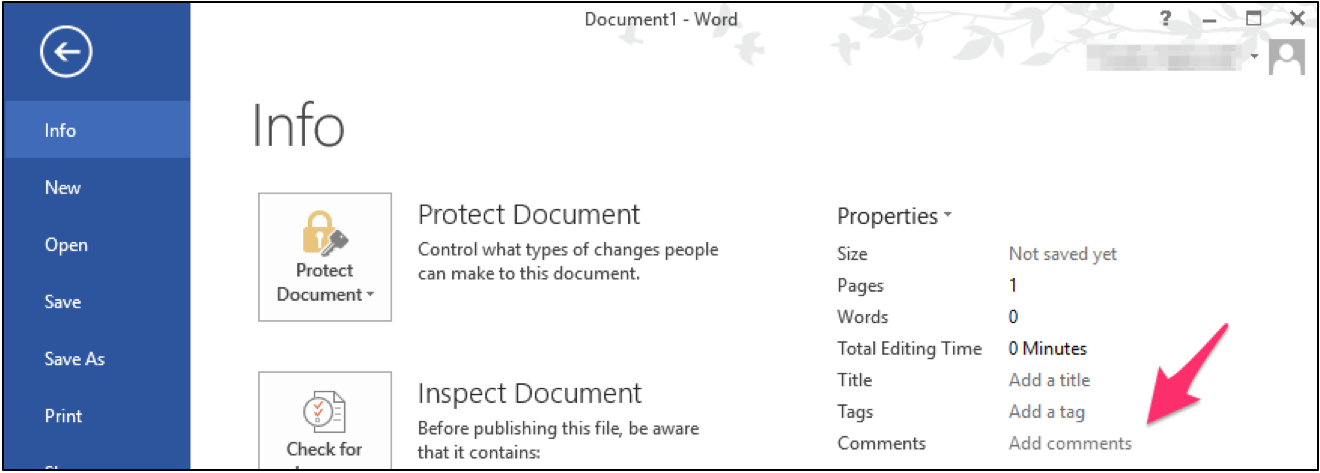
Carrie Roberts* // Can you think of a reason why you might want to put a lengthy comment into the properties of an MS Office document? If you can, then […]
The post Hide Payload in MS Office Document Properties appeared first on Black Hills Information Security, Inc..
Empire Resource Files and Auto Runs
Carrie Roberts* // I have added resource file and autorun functionality to PowerShell Empire. Empire now has the ability to run multiple commands at once by specifying the commands in […]
The post Empire Resource Files and Auto Runs appeared first on Black Hills Information Security, Inc..
Grepping Through PowerView Output
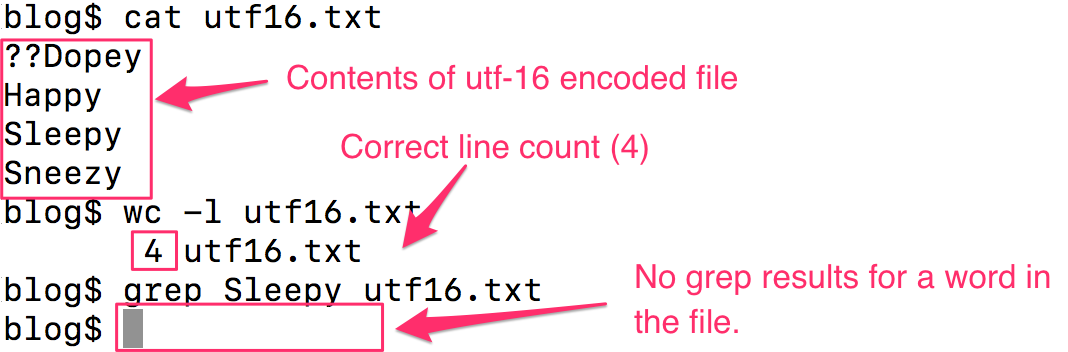
Carrie Roberts//* Have you found yourself trying to Grep through PowerView output, or any PowerShell output for that matter, and find that it returns no results for text you know […]
The post Grepping Through PowerView Output appeared first on Black Hills Information Security, Inc..
How To: Empire’s Cross Platform Office Macro
David Fletcher // During our testing, we encounter organizations of various different sizes, shapes, and composition. One that we’ve run across a number of times includes a fairly even mixture […]
The post How To: Empire’s Cross Platform Office Macro appeared first on Black Hills Information Security, Inc..
How to Bypass Web-Proxy Filtering

Brian Fehrman // Someone recently posed a question to BHIS about creating C2 channels in environments where heavily restrictive egress filtering is being utilized. Testers at BHIS, and in the […]
The post How to Bypass Web-Proxy Filtering appeared first on Black Hills Information Security, Inc..
HostRecon: A Situational Awareness Tool

Beau Bullock // Overview HostRecon is a tool I wrote in PowerShell to assist with quickly enumerating a number of items that I would typically check after gaining access to […]
The post HostRecon: A Situational Awareness Tool appeared first on Black Hills Information Security, Inc..
Bypassing Cylance: Part 4 – Metasploit Meterpreter & PowerShell Empire Agent

David Fletcher // The following techniques serve to illustrate methods for obtaining C2 communication in a particular Cylance protected environment. The configuration of the centralized infrastructure and the endpoint agents […]
The post Bypassing Cylance: Part 4 – Metasploit Meterpreter & PowerShell Empire Agent appeared first on Black Hills Information Security, Inc..